NIST Unveils Guidelines to Enhance Security of IoT Devices
It’s an established fact that devices connected to the Internet of Things may pose a threat. Look no further than last month’s distributed denial of service (DDoS) attack that hit domain name system provider Dyn, which crippled access to major internet sites and services. Now, the National Institute of Standards and Technology wants to do something about it: Make IoT devices more secure before they are built and keep them equally safe after they’re deployed.
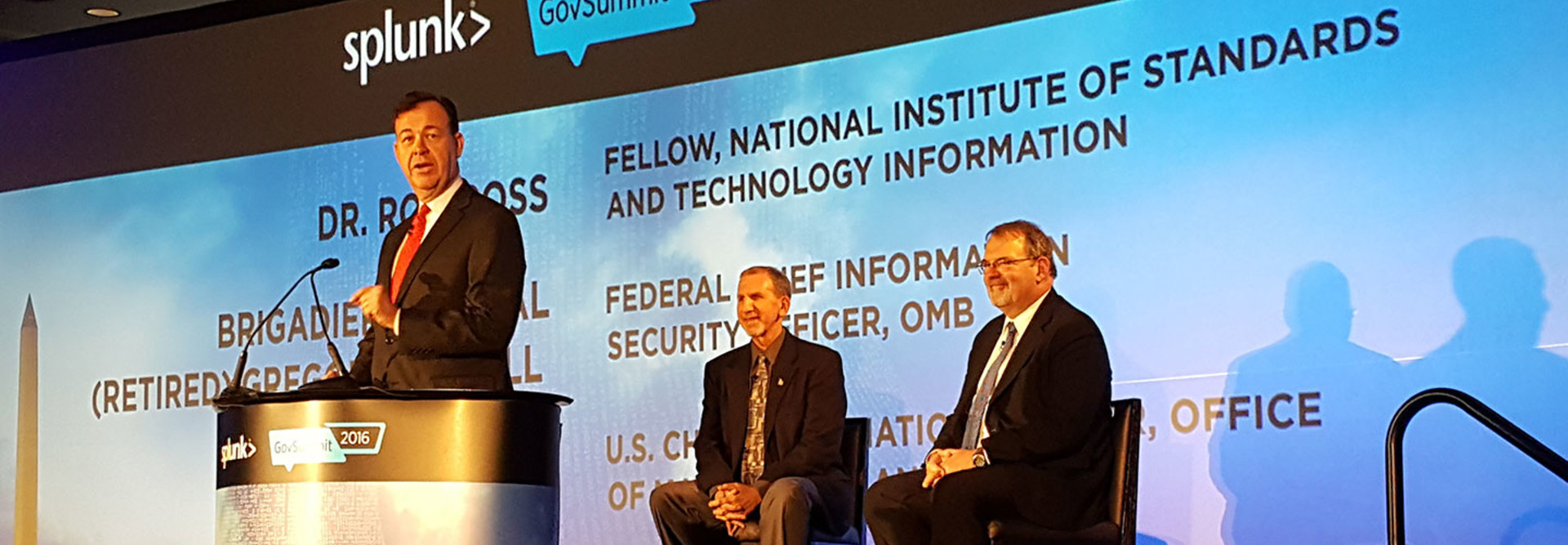
NIST issued wide-ranging guidance this week on how to engineer security for connected devices, which are designed to enhance the trustworthiness of IoT devices. Ron Ross, a fellow at NIST who co-authored the guidelines, unveiled the report at the Splunk GovSummit in Washington, D.C.
The goal of the voluntary guidelines, Ross said, is to give agencies and companies the same confidence in the trustworthiness of IoT devices that people have when they “cross a bridge or get into an airplane.”
SIGN UP: Get more news from the FedTech newsletter in your inbox every two weeks!
Building Trust in IoT
“That trustworthiness doesn’t happen by accident,” he said, adding that the security needs to be enabled at a systems-engineering level and not bolted onto devices after the fact. The guidelines are designed to make it more difficult for attackers to exploit vulnerabilities in IoT devices and mitigate any damage they do inflict if systems are compromised. “We want to make systems and components as resilient as they can be,” Ross added.
Appearing at the summit with Ross was federal CIO Tony Scott, who said that cybersecurity has been a major concern of the Obama administration and will be so in the Trump administration.
Additionally, Greg Touhill, the first federal CISO, spoke with Ross and Scott and said that “this is an inflection point for all of us.” Touhill said that embracing “security by design” is critically important. “This publication sets the flight plan for us to do that together,” he said.
Often, Touhill said, security is not designed into connected products from the start; many in the private sector assume it is a feature that can be turned on later. The NIST guidance looks at the processes of creating these devices and ensures that the right requirements are in place. “It’s a valuable document that is going to help us change the conversation from one of reacting to leading,” he said.
New IoT Security Guidelines
The guidelines, Ross said, are not built around cybersecurity but instead on systems engineering — how devices get conceived and built. They start with, and build upon, a set of well-established international standards for systems and software engineering published by the International Organization for Standardization (ISO), the International Electrotechnical Commission (IEC), and the Institute of Electrical and Electronics Engineers (IEEE). The guidelines will “infuse systems security engineering methods, practices, and techniques into those systems and software engineering activities.”
They take a “lifecycle-based” approach, Ross said, looking at each stage of the engineering process: the initial business analysis, the stakeholder requirements, and finally the design and architecture of the devices.
NIST used NASA as a model when designing the new guidelines, Ross said, because the space agency designs highly complex systems that require high degrees of reliability. The goal is to make systems that are more resistant to penetration and more difficult for attackers to sustain breaches if systems are penetrated.
The guidelines are just a starting point, Ross said. To enhance security, the government will need to work with industry and academia to influence the next generation of engineers, ensuring that security is built in to IoT devices from the start. “This is the start of a national dialogue,” he said.
The guidance is also applicable for legacy systems and devices as well as new systems under development, Ross said. Existing devices can be upgraded via software updates, or can be redesigned.
How to Get Agencies and Companies Involved
The Dyn attack exposed a critical danger: IoT devices whose default passwords had not been changed could be hacked, and subsequently used to form a botnet that overwhelms critical internet infrastructure with traffic, making it impossible for users to reach websites and services. Ross said some consumers may not know how to change those passwords, and IoT devices could be designed to force customers to change the passwords when they are first connected. That will add cost, forcing developers and companies to decide whether they should add that capability to IoT devices.
Splunk’s chief technology officer, Snehal Antani, said the current cost of launching a cyberattack is roughly one one-thousandth what it costs to defend. The NIST guidelines, he said, are designed to change the economics of cybersecurity. “You have to operate with security by design,” he said.
In addition to designing more secure devices, there are other steps the government can take to boost IoT security, said Ann Barron-DiCamillo, the former head of the Department of Homeland Security's U.S. Computer Emergency Readiness Team. She told FedTech that there needs to be public-private partnerships with internet service providers and network infrastructure vendors to monitor and stop traffic that could be taking advantage of hacked IoT devices. She also said that devices need to be patched seamlessly and in a transparent manner, but perhaps in a way that takes it out of the hands of the user.
“There is no one solution to this problem. And it’s not going to happen overnight,” Barron-DiCamillo said. “This is going to be a continued area of focus for months, if not years, to come.”
BlackBerry CISO David Kleidermacher praised NIST’s work as necessary, but told FedTech that the standards lab is not doing enough to make sure agencies and companies are actually following the guidance.
“NIST is spending an amazing amount of money and promoting these best standards, and doing almost nothing to have conformance assessment programs,” he said. “They should work with us and other leaders in security to develop programs that works economically, that gives you a good assurance per dollar.”
Government needs to work with security vendors to build practical security assessment programs, he said. In security, Kleidermacher said, government cannot hope that agencies and companies will follow up on the guidance. “Hope is not a strategy,” he said.