90 Percent of Feds Use Mobile Devices for Work, but Just 11 Percent of Those Devices Are Secure
In a perfect world, public-sector employees secure their mobile devices with complex passwords that are changed frequently, follow the protocols set forth by their agency’s IT department and don’t access sensitive data on insecure Wi-Fi networks. But we all know that isn’t the case and that mobility is a growing security threat to the government.
Cisco and the Mobile Work Exchange have teamed up to study these risky mobile trends in a new survey titled “The 2014 Mobilometer Tracker: Mobility, Security, and the Pressure In Between.” Responses from 30 different agencies, including the Homeland Security Department, FEMA and the Justice Department, point to weaknesses in some of the government’s most sensitive agencies. Here are a few highlights from the survey, which can be downloaded here.
Users Are Often the Weak Link
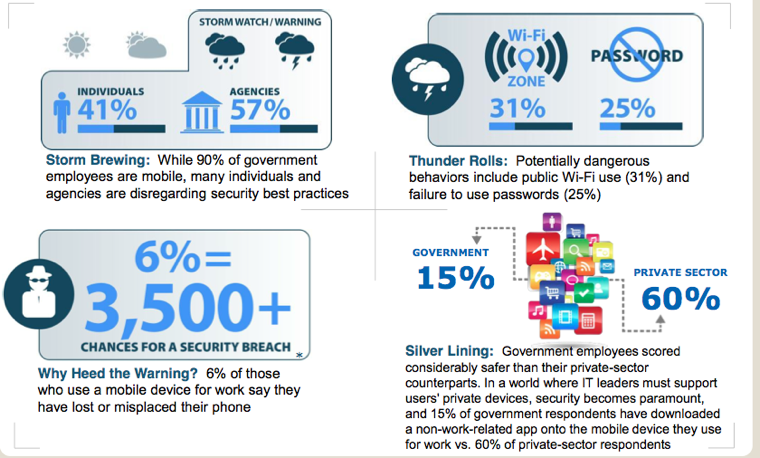
If your agency provides continuing education for users and has robust telework and bring-your-own-device (BYOD) policies, you are halfway to a secure mobile program. As most IT leaders know, and as this survey emphasizes, users are often the weak link. They don’t password-protect their devices, and some users connect over public Wi-Fi networks. Convenience is a major driver of risky behavior that can only be prevented with ongoing, meaningful education. According to the survey, at least 90 percent of government employees use at least one mobile device (a smartphone, a tablet or a notebook) for work, and at least 15 percent of those devices are personally owned. In fact, only 11 percent of federal employees are adhering to mobile security best practices.
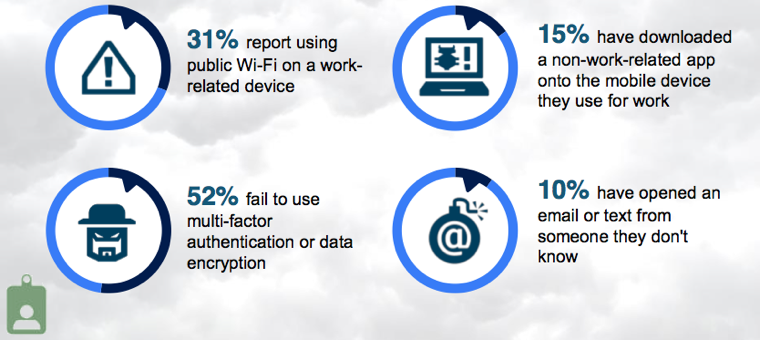
The chart above underlines some of the worst offenses and points out that many, if not most, federal employees are walking on thin ice. The blame, however, does not fall squarely on the shoulders of the users. A full 26 percent of feds have never been trained on mobile security, even if they have a government-owned device or a personal device that can access government networks. That is a condemning number for a government that has access to some of the world’s most sensitive data.
The government has made great progress on teleworking, but it’s being complicated by BYOD — and now BYOC (bring your own cloud).
Going forward, the Mobile Work Exchange offers these tips for feds and agencies:
For Individuals:
- Always use a password on all mobile devices. Make it complex and change it often
- Always use a secure wireless connection
- Never open an email or text from someone you don't know
- Do not store personal info – address, credit card number, etc. – on a mobile device
- Adhere to security and IT training provided by your organization
For Organizations:
- Establish a formal employee-focused mobile device program, including written mobile device security policies
- Create regular training and require all employees to participate in training
- Require all devices to utilize a password
- Install multi-factor authentication or data encryption on mobile devices to secure organization data
- Implement a remote wipe function for lost or stolen devices
To read the study in full, check out MobileWorkExchange.com.










