Agencies Adopt New Cybersecurity Tools in the Post-Snowden Era
When Edward Snowden leaked sensitive government information to the press in 2013, officials estimated the stash included millions of files from the Defense Department and National Security Agency, an unquestionably damaging haul.
Since then, driven by fear of a Snowden-like breach, agencies all across government have adopted new technologies and adjusted their cybersecurity strategies to protect billions of federal records from a similar fate.
“We’re always looking at incidents of intrusion to learn from them,” says Dominic Cussatt, acting CISO at the Veterans Affairs Department. “We’re trying to revisit our holistic cybersecurity program around events like the Edward Snowden incident and many others.”
In September, the House Intelligence Committee released an unclassified version of its report on the events leading up to the Snowden breach. In it, investigators described what feds can learn from the fallout.

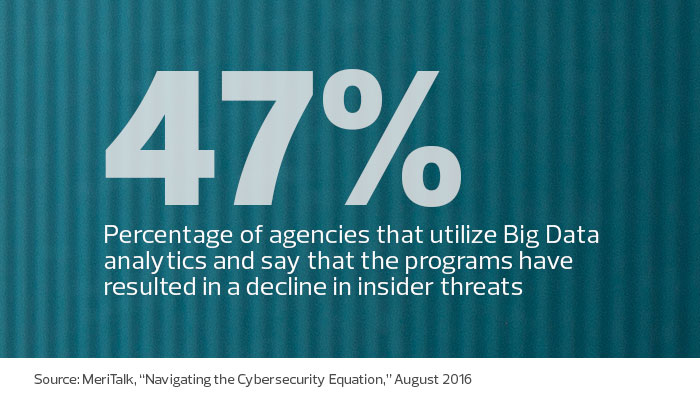
In addition to condemning Snowden, the document lists several steps agencies can take to improve protection against insider and external threats, including new software and cyberhygiene practices. But in the years between the hack and the report’s release, many agencies had already aggressively started their own response and studied ways to prevent a similar breach.
Cussatt worked at the Defense Department in 2013, providing him a firsthand view of the damage inflicted by a determined insider with far-ranging access.
“If we learned anything from the Snowden event, it was that it’s now very clear what the threat is,” Cussatt says. “It reminded us that we need to pause and think, ‘How do we leverage this great technology, but also harness the vulnerabilities that this great technology can cause for us?’ ”
James Stanger, a senior director at CompTIA, says the Snowden breach led to a “sea change” in how agencies think about cybersecurity. “Before, a lot of organizations inside and outside of government had ‘stranger danger,’ ” he says. “They wanted to make it so people couldn’t get in, but they weren’t really thinking that insider threats could happen to them.”
Reducing Cybersecurity Risk
The House report concedes that IT leaders face an impossible task in trying to eliminate the threat of “another Snowden,” but it outlines several steps agencies can take to substantially reduce their risk. This includes using software to automatically detect scraping tools, disabling access for removable media on many machines and adding two-person control permissions to transfer large amounts of data. The report also suggests reducing the number of privileged users for each network and requiring more multifactor authentication.
Many agencies had already turned to some or all of these tools, but Cussatt says that incidents like the Snowden leak have spurred agencies to strive for a more consistent approach. In 2015, the VA evaluated its security measures and developed a strategic plan with 3,000 items, including steps to ward off insider threats, Cussatt says.
Since then, Cussatt says the agency has taken more dramatic steps, including fully implementing two-factor authentication for remote access, reducing elevated network privileges by 95 percent and removing 14,000 instances of prohibited software.
“It’s getting harder and harder for the [malicious] insider to have any kind of access,” Cussatt says.
Taking a Layered Security Approach
Chris Wlaschin, CISO at the Health and Human Services Department, says his agency has made “tremendous strides” in increasing its ability to detect and respond to cyberattacks. As an example, he says the department has exceeded the federal targets for Personal Identity Verification protections for privileged and unprivileged users. HHS is also implementing the first of the four-phase Continuous Diagnostics and Mitigation cybersecurity program led by the Department of Homeland Security. That program provides agencies with tools and capabilities to regularly identify and mitigate risks.
“These efforts have been expanded to include multiple layers of cybersecurity, numerous technologies, processes, and programs to address vulnerabilities and increased information sharing with federal partners and the health sector,” Wlaschin says.
While agencies are reticent to explain their new processes in detail, IT leaders say they follow an incremental approach to bolster security and minimize risk.
Gregory Wilshusen, director of information security issues at the Government Accountability Office, says the cybersecurity audits he leads sometimes find agencies failing to take basic steps that could help protect systems and information. For example, some departments have trouble patching software in a timely manner. “We find that these patches are not being installed, sometimes for months or years, and that creates risk for the organization,” he says.
In other cases, Wilshusen says, administrators share user accounts, a textbook no-no “that diminishes the ability of an organization to trace system activity to specific individuals.”
Even agencies facing scrutiny sometimes have difficulty maintaining their cybersecurity measures. The Snowden report mentions, for example, that several “Secure the Net initiatives” (such as two-stage controls for systems administrators) had not been instituted at some agencies more than a year after the Snowden breach.
Don't Let Security Stop the Mission
One common trait of agencies that consistently stay atop cybersecurity issues, Wilshusen says, is leaders who emphasize its importance. “If support at the top isn’t there, that could have an impact throughout the organization,” he says.
Larger departments sometimes struggle to maintain strong protections across their networks. “The bigger ones have more difficulty, in part because their systems are much more complex, geographically dispersed and technically diverse,” Wilshusen says. “That presents additional challenges.”
Across industries, one major stumbling block in implementing cybersecurity solutions is finding a way to do so that doesn’t impede the larger mission of the organization. “You want to react quickly, but you don’t want to react so hysterically that you bring the mission to a halt,” Cussatt says. “Nothing makes a system more secure than disconnecting it from the network, but we just couldn’t do that with our information repositories.”
At the VA, Cussatt says, some users initially resisted new security measures they viewed as cumbersome. However, he says, users eventually saw the value of protecting not only agency information, but also their own identities, through practices like multifactor authentication. “At the beginning, there is annoyance, perhaps, and a little discomfort,” Cussatt says. “But if we’re doing the right thing, it eventually sinks in, and they realize that this is a better way to do things.”