DOD Owns the Technology for Zero Trust but Must Learn How to Use It
The White House has mandated that civilian federal agencies implement zero trust by September 2024. The DOD’s Zero Trust Strategy and Roadmap is set for completion by fiscal year 2027.
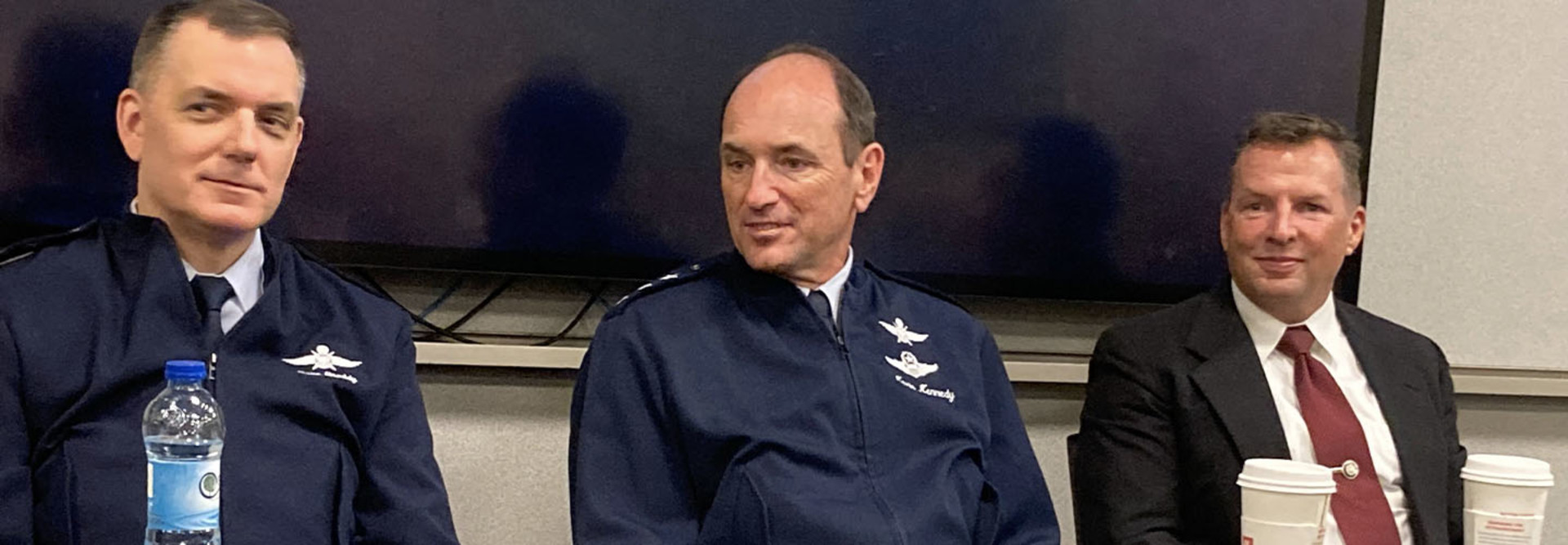
Military installations are protecting more than just their networks; they’re also watching out for their applications, systems, platforms and airmen working within the network, said Lt. Gen. Kevin Kennedy, commander of Air Forces Cyber.
“Our standard boundary defense is defense in depth,” he said. “Now, what we’re going to be driving toward is awareness in depth.”
The transition to the cloud has created tremendous opportunities to pull data from the edge and “find that needle in that stack of needles of bad behavior on a network,” Snoddy said.
“But we have not kept up with the workforce side in actually understanding how to do anything with that [massive] sea of data.”
Those working in cyber may have the technology to collect all of the data, he said, but they don’t always know what to look for in the data or what questions to ask.
“We need people educated within the DOD, or it could be contractors,” he added. “We just need to bring that talent into the department that knows how to make something of the data.”
EXPLORE: How CDW•G’s IT cybersecurity solutions can support your zero-trust environment.
Seek Outside Aid When Zero-Trust Deployment Gets Complicated
Procurement and acquisition can also create a mild roadblock, said Patrick Higby, a retired Air Force major general and consultant to a company providing zero-trust solutions. It’s not always clear to the procurement experts why a technology is necessary, he said, and that can cause delays.
“There’s a bit of a gap there. That’s just the nature of how the department is set up,” he said. “Then there’s a reluctance to take a big bite, and that’s where the opportunity exists.”
Zero-trust environments — or any major technology projects — don’t necessarily have to be built from scratch, Higby said. “Use something that’s already out there. A DOD- or Air Force-specific, unique zero-trust architecture is not going to work. Do the process and culture tweaks, and then start moving out.”
Squadrons at a loss for how to begin can and should seek outside help, he said: “There are many vendors that can help you.”
To learn more about DAFITC 2023, visit our conference page. You can also follow us on X (formerly Twitter) at @FedTechMagazine to see behind-the-scenes moments.