Cybersecurity is consistently one of the most talked-about areas of federal IT. The growing mobility trend has sparked a rapid growth of endpoints that must be secured, and bring-your-own-device (BYOD) programs mean that federal employees could be accessing sensitive data on unsecured devices. However, in order to keep productivity and morale high, IT departments are increasingly allowing users to work on their own devices both in the office and at home.
There is no simple recipe for security, which is why MeriTalk recently surveyed 100 cybersecurity professionals and 100 federal employees about their experiences working with security in government. The results are indicative of noncompliance and a failure to communicate effectively.
Here are some of the most notable statistics from the report, which can be downloaded here:
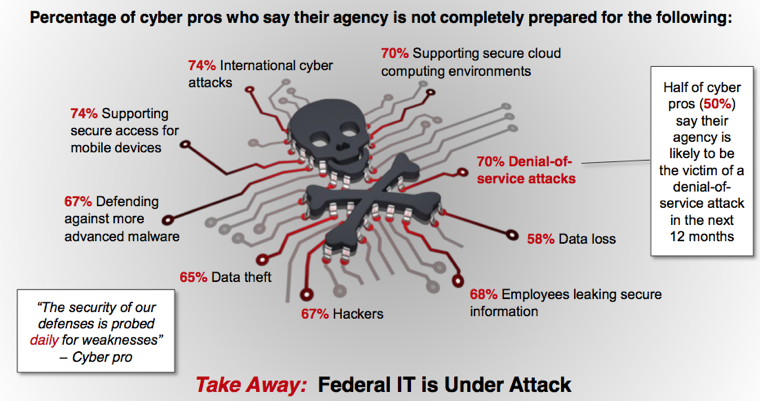
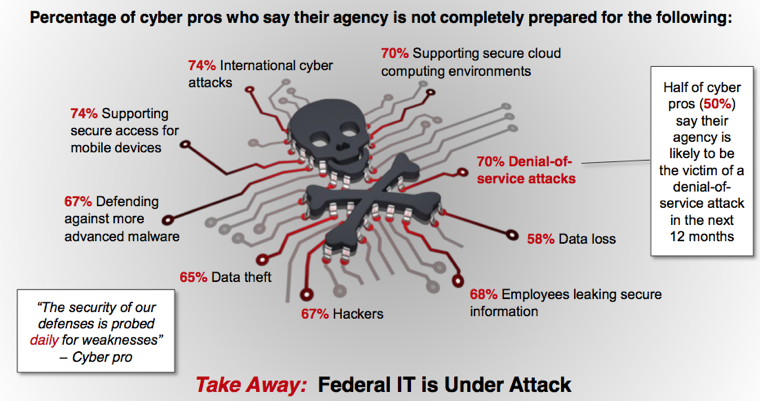
50% of cybersecurity experts say their agency is likely to be a target of a denial-of-service attack in the next 12 months.
49% of agency security breaches are caused by a lack of user compliance.
69% of users say at least some portion of their work takes them longer than it should due to security measures.
31% of end users say they use some kind of security work-around at least once a week.
74% of cybersecurity professionals say their agency is not ready to support secure access from mobile devices.
67% of cybersecurity professionals say their agency is not ready to fend off hackers.
74% of cybersecurity professionals say preventing data theft is their top priority.
40% of cybersecurity professionals say ensuring a user-friendly experience is a priority.
54% of users struggle to keep track of their passwords.
26% of cybersecurity professionals say they are completely prepared for an international attack.
95% of end users and cybersecurity professionals believe the deployment of cybersecurity measures is an absolute necessity to protect agencies from data loss, data theft, and denial-of-service attacks.