COBOL and Outdated Technology Cited as Factors in OPM Hack
The news earlier this month that the personal data of more than 4 million current and former federal employees may have been exposed as the result of a data breach at the Office of Personnel Management (OPM) has left the federal IT community searching for answers.
Congress had leaders from the OPM and other agencies on Capitol Hill on June 16 to answer detailed questions about the hack, including how it happened and, more specifically, why encryption technologies weren’t in place to prevent the hacks.
OPM CIO Donna Seymour explained that the agency’s archaic IT infrastructure was a barrier to implementing more modern security measures that might have helped to mitigate the hack.
“A lot of our systems are aged, and implementing some of these tools takes time, and some of them we cannot even implement in our environment,” Seymour said during her congressional testimony.
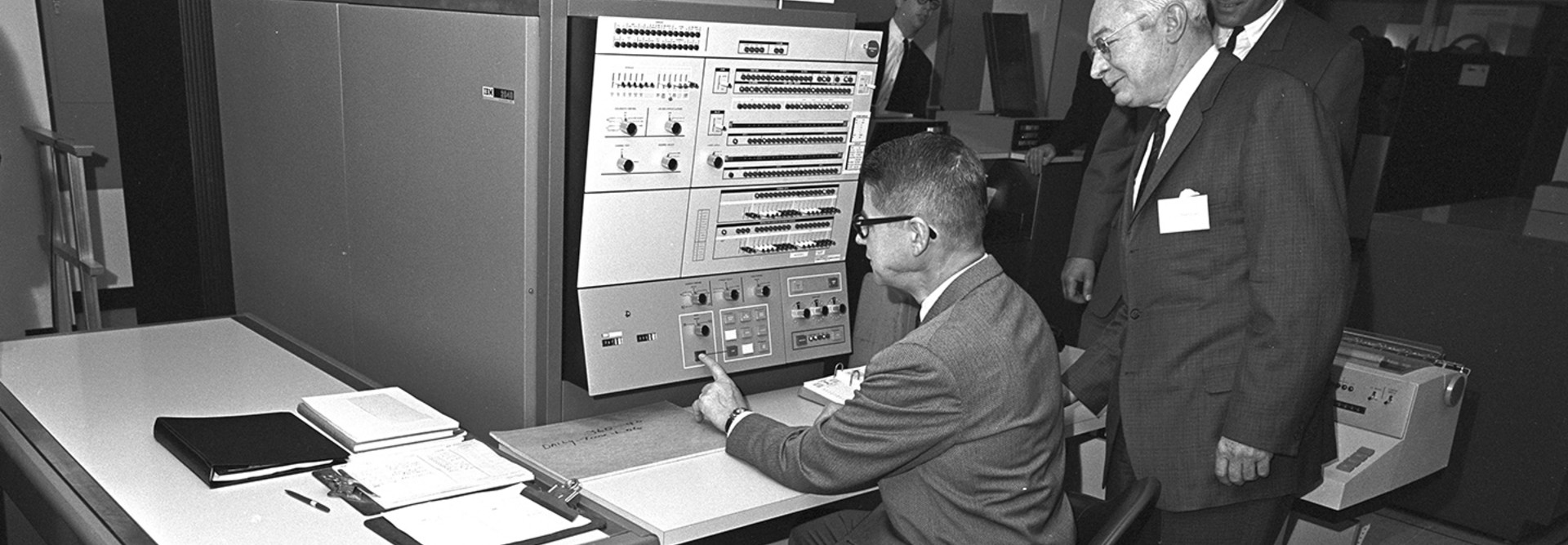
More specifically, the OPM is facing a huge problem with modernizing its security measures and tactics because of one acronym: COBOL. The programming language that rose to prominence in the 1960s is rampant throughout the OPM and with the advanced persistent threats federal agencies are experiencing, it’s a significant vulnerability.
“These are systems that have been around for going close to 25 to 30 years. They are COBOL systems,” said Seymour.
As FedTech reported last year, use of COBOL in the federal government is widespread, and many agencies, not just the OPM, must wrestle with how to modernize their IT and transition away from legacy technology like COBOL. The Social Security Administration, for example, had about 60 million lines of COBOL code in production, according to a Government Accountability Office report last year.
Federal CIO Tony Scott echoed Seymour on the need to replace or upgrade aging IT infrastructure and software sooner rather than later.
“Probably long term, the biggest thing is to double down on replacing these legacy, sort of old systems that we have. One of the central problems here is you have old stuff that just was not designed or built in an era when we had these kinds of threats, and in some cases, it’s very, very hard to duct tape and Band-Aid around these systems,” he said during his testimony.