The Intelligence Community Balances New Tech with New Threats
The intelligence community takes advantage of cutting-edge IT every day to ferret out threats and protect national security, but terrorists’ increasing access to modern communication, encryption and other technologies also increases the nation’s vulnerabilities, according to intelligence officials.
Speaking earlier this month at the Intelligence & National Security Summit in Washington, D.C, officials from multiple intelligence agencies said they must do more to share data and technology tools to combat threats.
“That’s why a number of us are involved in some transformational activities inside our organizations, so that we can adapt to a new operating environment,” CIA Director John Brennan said, according to FCW.
Indeed, the CIA launched the Directorate of Digital Innovation in the fall of 2015, which was the spy agency’s first new directorate since 1963. The DDI is charged with infusing digital and cyber capabilities throughout the CIA and overseeing the career development of the agency’s digital and cyber experts. Additionally, the DDI is responsible for making sure the CIA’s digital technology keeps pace with rapid technology innovations and cybersecurity trends.
Balancing New Tech with Emerging Threats
According to defense IT journal C4ISRNET, Director of National Intelligence (DNI) James Clapper said at the conference that while technological change can bring positive developments, “it’s difficult to predict how technology will affect national security [in] tech areas like artificial intelligence, health care and agriculture.”
Encryption benefits the intelligence community, yet the same technologies used in cybersecurity across the federal government can also enable terrorist activity, something FBI Director James Comey has repeatedly highlighted.
“We're facing this ‘going dark’ phenomenon where we cannot see these people in the way in which they are communicating,” Comey said at the conference, according to FCW. “I love end-to-end encryption. I don't want anybody looking at my stuff. I don't want anybody looking at my banking information, my healthcare information.”
Comey told FCW that encryption can keep Americans safe from cyberthreats, but can also hamper law enforcement, adding that the different sides of that debate need to work more constructively together.
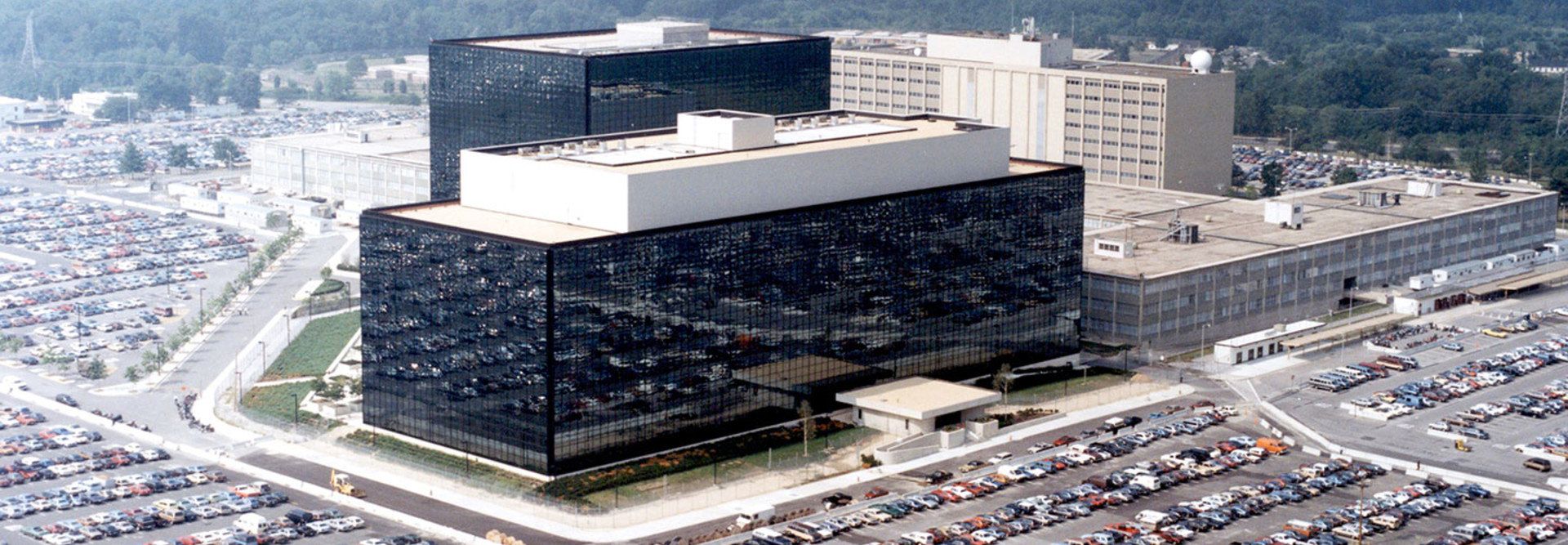
“This has become such a charged emotional issue that we’re not really having that dialogue and we’re not getting into what's in the realm of possible,” Navy Adm. Michael Rogers, commander of U.S. Cyber Command and director of the National Security Agency, said, according to FCW.
Dual-Use Technologies May Pose a Threat
A RAND Corporation report, released in July, found that many modern commercial technologies — including mobile communications, Radio Frequency Identification devices, biometrics and Big Data analytics — are “persistent and are dual-use, which means that they can benefit society or harm it. Although they are intended for commercial purposes, such as learning about shoppers’ preferences and finding new markets, they can easily be used by police and security services to identify and track criminals, terrorists, insurgents, and spies. This means that these technologies have the potential to disrupt military intelligence operations and to jeopardize the plans, actions, and security of the warfighter.”
For example, intelligence agencies can use data analytics to detect whether someone using an alias is hiding their true identity by mining the “digital exhaust” they leave “through social media, commercial purchases, gaming, and other activities.” At the same time, “these capabilities can be combined with historical and cultural data to help project, if not predict, the movements of enemy forces.”
At the same time, intelligence agencies recognize the need to get new IT and applications to their analysts faster. “We’ve come to understand that the way we built systems in the past, the way we developed applications, the way we brought [information technology] to the analysts’ desktop, won’t work in the future,” Robert Cardillo, director of the National Geospatial-Intelligence Agency said at the conference, according to a Pentagon statement. “It’s not agile, it’s not responsive enough, it’s not timely.”
Intelligence agencies are essentially using DevOps, with smaller teams focused on specific tasks to create development capabilities next to operational capabilities. “We call them rapid-feedback teams, small groups of dedicated analysts, IT specialists, data scientists, computer programmers that work on a problem set, an intelligence outcome,” Cardillo said. “As they’re working on that technical capability, they’re getting that immediate feedback from the analyst about what’s working and what’s not.”
Cardillo said that work is being done at both classified and unclassified levels. “It’s the necessity of the mission that’s going to drive us forward, Cardillo said. “How quickly can we scale that from those small teams to the large teams. Some of that is a component of the budget but we’re doing it as quickly as we can.”
The Importance of Technology Cooperation
Meanwhile, Clapper stressed the importance of cooperation via the Intelligence Community Information Technology Enterprise, or ICITE, which the DNI established in 2012.
The ICITE program has established a common desktop for users to work from, an App Mall from which users can download community applications, and the IC Cloud for data storage. It provides a common set of standards and platforms, as well as security protocols, and allows analysts from one intelligence agency to analyze data collected by another.
C4ISRNET reports:
“Clapper said ICITE is trying to take the IC to the next level of integration and information sharing, adding it’s not just about an IT upgrade, but more about making a fundamental change in the way the IC operates in terms of processes and people. He also said he expects ICITE to last beyond his and the current administration’s tenure. He said that one of the reasons he stayed at his post as long as he did — at six years, longer than any of his predecessors — was to ensure ICITE could be so entrenched as to not be undone.”