The Next BYOD Challenge for Feds: Wearables
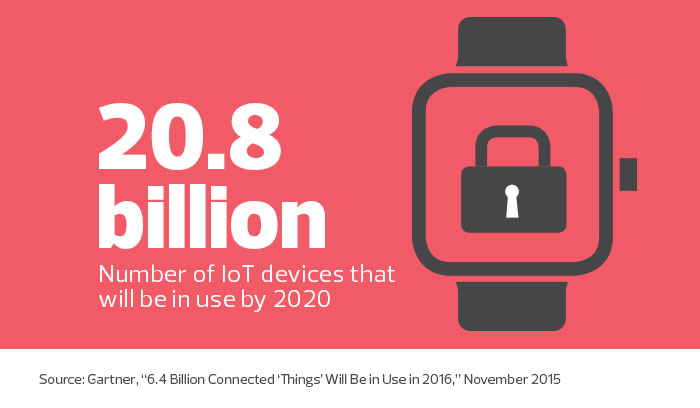
From smart specs and fitness bands, to smart watches and medical instruments, consumers are engrossed by the next generation of wearable devices equipped with sensors and internet connectivity.
The devices also entice federal leaders, who imagine a flurry of benefits with wider adoption. Think of the advantages for first responders, who might instantly relay information about their environment and their health to a command in real time.
Unfortunately, many of today’s wearables arrive with major security weaknesses and — in a worst case scenario — lack security features altogether. But agencies can still take advantage of the new capabilities by establishing solid security practices and recognizing the inherent security weaknesses that accompany the popular wearable technology.
Treat Wearables like Other Devices
As innovation accelerates, wearables will find broader application, and their functions will become more exciting. While many agencies already take advantage of the gadgets, and others will find future iterations more valuable (from a security standpoint), all federal organizations should treat the devices just as they would any other computing device.
That means IT officials should conduct risk assessments on the potential security weaknesses of each model, including which threats each model may face and how to mitigate them. Assessments should include the security of a device’s Bluetooth low-energy transmission as well.
At the same time, agencies should update policies and procedures to include wearables. In some cases, security officials may need to ban, or at least limit, the use of specific devices not proven to be safe. Agency leaders may want to incorporate security as a major factor in any future purchase of wearables.
As a starting point for these changes, the National Institute of Standards and Technology recently released an extensive list of security guidelines for Internet of Things devices, which also applies to wearables.
The Department of Homeland Security’s “Strategic Principles for Securing the Internet of Things (IoT)” also details high-level best practices for securing any IoT-connected device, and includes recommendations on uniquely identifying and authenticating devices.
Consider Implications of Outside Wearables Coming In
The surge in popularity of wearables is somewhat analogous to the bring-your-own-device movement that agencies have faced in recent years. In both cases, IT leaders have little to no control over the devices, and almost no visibility into what they do.
Almost certainly, employees, contractors, vendors and partners are already wearing connected, personal devices while conducting agency business. That’s why it’s important to act on wearables now.
While many devices do not pose a risk to agencies, a compromised device could allow an attacker to access data from the wearable’s sensors — including cameras, microphones and location services. If a wearable is not well secured, it could store or transmit sensitive data with weak or nonexistent security measures, making it susceptible to interception or tampering. As a result, agencies may need to consider prohibiting the use of some, or all, types of wearables.
Bolster Wearables' Inherent Security
Security loopholes should not dampen the promise of wearables for federal agencies. IT leaders can play a critical role in improving the devices’ inherent security by working with industry to develop best practices, guidelines and security standards. DHS recently suggested that developers and IoT manufacturers make devices more secure by default, and provide built-in, robust capabilities for secure device use and maintenance.
Suzanne Schwartz, associate director for science and strategic partnerships at the Food and Drug Administration’s Center for Devices and Radiological Health, has been one of the leaders in shaping the government’s position toward wearables.
“Addressing the impact of medical device cybersecurity on public health takes input and effort from many stakeholders. The FDA cannot do this alone,” she says of her agency’s approach to IoT medical devices. “Engagement among device manufacturers, other government agencies, healthcare delivery organizations, patients and security researchers is the cornerstone of our approach to addressing cybersecurity throughout a medical device’s total product lifecycle.