Why Shadow IT Now Gets a Second Chance from CIOs
For years, the unvetted and unauthorized technology known as shadow IT has been the scourge of federal IT shops. But more agencies now believe the often surreptitious technology can help in nontraditional ways.
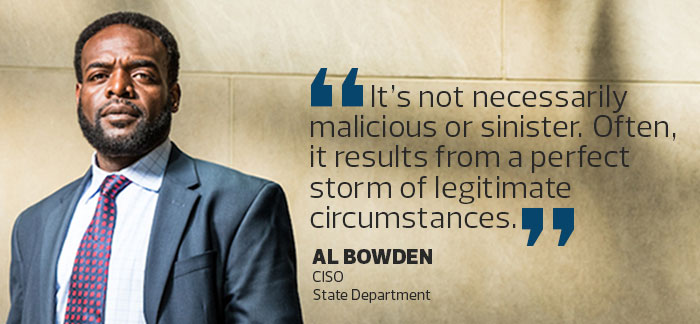
“It’s not necessarily malicious or sinister,” says Al Bowden, CISO at the State Department. “Often, it results from a perfect storm of legitimate circumstances.”
With that in mind, Bowden’s staff have increased their monitoring of unsanctioned hardware and software. They also are working more closely with the entire department to identify technology gaps in hopes of eliminating shadow IT.
The State Department’s nuanced approach is a model for agencies struggling with the issue, according to IT consultants and security experts at the National Institute of Standards and Technology (NIST). This philosophy, they say, can reduce security risks and provide insight into how to improve day-to-day operations.
Adopting this ideology occasionally requires some soul-searching.
“IT leaders sometimes must look in the mirror and ask if we’re being responsive enough to the organization,” Bowden says. “Is there more we should be doing to help end users better understand the governance process that’s in place to address their needs?”
Before they can reap the hidden rewards of shadow IT, CIOs first must understand the dangers it presents. Security tops that list.
SIGN UP: Get more news from the FedTech newsletter in your inbox every two weeks!
What Are the Root Causes of Shadow IT?
“Shadow IT creates blind spots, which means organizations incur risks without the knowledge of the CIO or CISO,” says Matthew Scholl, chief of the computer security division at NIST.
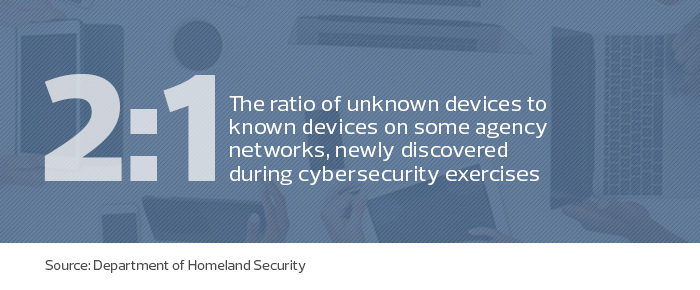
The gaps can appear in hardware or software. Kevin Cox, the manager for the Department of Homeland Security’s Continuous Diagnostics and Mitigation (CDM) program, says agencies are using tools, such as hardware and software asset management, to discover uncataloged devices. This year, IT leaders found, on average, 44 percent more devices on agency networks than expected.
At the same time, experts point to a common example of shadow IT: file sharing via cloud services. Popular, consumer-grade services don’t provide the advanced security controls often available with paid, enterprise versions. Worse, sensitive data shared via free software can be vulnerable to hackers.
“At no other time in the past has such a rich menu of software services and solutions been available to people,” says Kimberly Hancher, former CIO at the Equal Employment Opportunity Commission and now an industry consultant. “That gives program managers a means of configuring IT tools to meet their business needs simply by breaking out a credit card.”
Otherwise careful users often succumb to shadow IT simply because of unfamiliarity with the agency’s policies. Another reason: Workers do what it takes to get the job done, regardless of whether agencies provide the tools users need.
“Shadow IT doesn’t just happen. It’s usually the result of an organization trying to support its mission in the most efficient way possible,” Scholl says. “Unfortunately, those actions may be misguided because they don’t look at the risks holistically.”
How to Address Shadow IT in Your Agency
Security experts suggest a two-pronged approach for addressing shadow IT. First, identify unauthorized software, cloud services and hardware as quickly as possible. A variety of resources can help. NIST’s Cybersecurity Framework and its Risk Management Framework offer guidelines for identifying assets (such as hardware and software), risk-profiling data, and other key steps.
Homeland Security’s CDM program provides insight and tools, such as configuration management, for identifying, prioritizing and monitoring cybersecurity risks, including shadow IT.
Commercial tools can also help staff determine what’s running in their enterprises. Those solutions, which include suites from Dell, Centrify, Splunk and Symantec, can then suggest security strategies for what they found.
But technology alone won’t fully address the rise of shadow IT. Some IT teams are working more closely with agency staff to find answers.
For example, the State Department created a process that helps users formally request new capabilities and receive a response within a specific time frame. The department also formed a cloud computing governance board. When there is a bona fide need for shadow IT by a large percentage of users, the board can help CIOs and CISOs identify funding and then choose a solution that becomes the agency standard, Hancher says. “The agency should authorize it, certify it, bless it, implement it, train the workforce to use it and lock out competing solutions,” she says.
Update and Clarify Agency IT Policies
Cox notes shadow IT can even help agencies in some cases. “The key for us is looking at the idea of ‘shadow,’” he says. “There shouldn’t be shadows in the network for leadership. But how does that get reported? That’s up to system leadership.”
For example, he says, some agencies may not want the details of all their systems broadcast throughout government, but as long as IT officials understand who is using their networks — and how — those uses may pass muster.
Hancher also advises agencies to update their policies for acceptable use to align with today’s technology. “Many of these policies are out of date in the bring-your-own-device age, with the wide availability of cloud services and apps,” Hancher says. This can provide clarity about acceptable tools and their proper use. “It’s important to be clear about the proper procedures for requesting a service or solution that’s an exception to the rules.”
Since changing how it thinks about shadow IT, the State Department has benefitted. When it launched a cloud governance board last year, the risk of cloud-related shadow IT in the department was “significantly higher,” Bowden says. Today, that level is lower based on fewer shadow IT incidents discovered.
“We’ve gotten out the message about the perils and dangers, and we’ve made the workforce aware of the vulnerabilities,” Bowden says. “There remain a few stragglers, but we think we’ve turned a major corner.”











