DHS, FEMA and USDA Officials Urge IT Focus on Outcomes, Risk-Taking
The term “digital transformation” gets thrown around a lot these days, says Michael Hermus, chief technology officer at the Department of Homeland Security. What does it actually mean?
Hermus, speaking Wednesday at FedScoop’s “Government of the Future” conference in suburban Washington, noted that DHS is most focused on the outcomes the agency is trying to accomplish Often in IT, he said, leaders and employees get distracted by “shiny objects” that help them get their jobs done, but they still need to be focused on outcomes.
Shifting the Tech Culture at DHS
In terms of digital transformation, DHS is focused on four key pillars. The first is engaging with department components and the public to reimagine how the agency can serve them. “We need to keep the mission and customer at the center of everything we do,” he said, and technology is there to help with that.
Second, DHS is working to empower employees via collaborations tools and technology to engage them and give them the skills they need to do their jobs well.
Third, Hermus said, is optimization of operations: Automation and engineering need to be combined to make DHS operations as efficient as possible.
And finally, the most difficult and potentially most powerful pillar, is transforming DHS products and services in the field.
Repeating something he had said previously, Hermus noted that DHS needs to be a “a tech company with helicopters, badges and security clearances.”
That shift is happening in the private sector, Hermus said, as manufacturing companies and retailers that did not see themselves as tech companies — or that did not see IT as a cost center — are having to become tech firms to compete. “It is a strategic differentiator even for nontech companies,” he said.
“If we’re going to do our mission as best as we possibly can, we’re going to have to have become very, very good at technology,” Hermus said.
There are areas in which DHS can improve, Hermus said. By focusing too much on mitigating risk up front, which is a sensible goal, IT managers can lose sight of creating innovative programs.
The federal bureaucracy exists for a reason, Hermus said; it’s difficult to change, and IT leaders can end up “suffocating under a crushing burden of processes” that may have been useful at one point but are duplicative and less useful now. A shift in mindset shift would allow IT leaders to break from the past, he said.
To make that shift, agencies need to promote collaboration instead of control, and focus on what they are trying to accomplish. “The digital transformation journey is just starting,” Hermus said. “I don’t think there is an end. What we’re trying to do is build the capability and capacity for constant improvement.”
“The future is a state of accelerating change,” Hermus added. “Organizational agility is the difference between innovation and obsolescence.”
EPA, USDA Officials Urge Risk-Taking in IT
Hermus’s sentiments were common at the event. At a separate panel, Jonathan Alboum, CIO of the Agriculture Department, and Adrian Gardner, CIO of the Federal Emergency Management Agency, said federal IT leaders have to acknowledge that there will sometimes be failures.
Gardner said IT leaders should start projects with the understanding that there will be failures along the way. When Gardner came to FEMA from the Energy Department, he conducted audits of agency’s IT inventory. Some field offices had never done that before or even met with the agency’s CIO, he said.
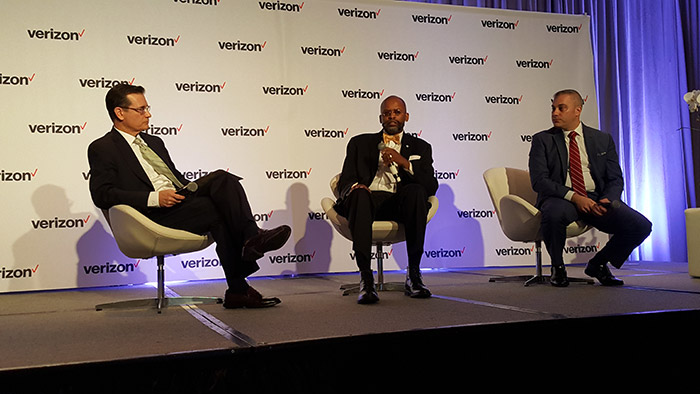
From left: Peter Pin, vice president of the public sector at Verizon; FEMA CIO Adrian Gardner; and USDA CIO Jonathan Alboum.
There was a notion that such audits could be done in a week, Gardner said, an idea that was “sadly mistaken.” FEMA had to innovate around that process. It was “truly an experiment,” he said, and his team had to “trust in the fact that I was going to get it done” and that there would be both success and failure in the process. Gardner said that federal IT leaders need to call failures out as such. “Never let them see you sweat,” he said.
Alboum said that in both private industry and government, there is always a chance that a project will be late or go over its budget. The key for IT leaders is to not let small failures snowball. They need to communicate with their staff and agency leadership, and potentially rework projects. If that doesn’t happen, that’s when there is “a government failure that makes the news and gets you in big trouble.”
In terms of managing risk versus reward, Alboum said that it’s important for security officers to get their concerns about, say, potentially risky software out in the open. That can help agencies make more informed decisions, as decisions get bumped up from IT to agency leaders such as undersecretaries, he said. That way, they will understand the impact of the work IT is doing and there will be broader ownership of those decision — and the potential reward that can come with them.
Gardner noted that he is the authorizing official for all FEMA systems, but that he spreads the risk in doing so around. He has an information system security officer and a designated authorizing official to help him sign off. “They have 49 percent of the risk acceptance. I retain 51 percent,” Gardner said to laughs.
Agencies need to collaborate and learn best practices from each other as they adopt similar technologies, Alboum said. “It’s hard to make those connections at times,” he said. “Where you as vendors see similarities, help us. Reach out.”