What Is Zero-Trust Security?
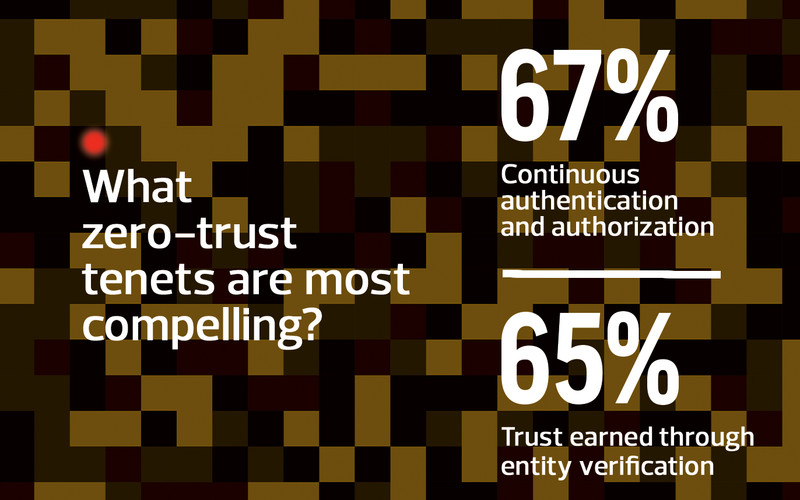
In August, the National Institute of Standards and Technology issued the final draft of Special Publication 800-207 on zero-trust architecture, which defines zero trust as “a cybersecurity paradigm focused on resource protection and the premise that trust is never granted implicitly but must be continually evaluated.”
Some in government — and in military agencies specifically — initially dismissed zero trust as little more than a new marketing buzzword, but have since become convinced of its benefits.
“The biggest misconception or misunderstanding is that zero trust is new,” says Scott Rose, a NIST computer scientist and co-author of the special publication. “The more you dig into zero trust, the more you realize this is an evolution of the trends that have been going on for a decade or more.”
These trends, he says, include the principle of least privilege, which gives people access only to the functions they absolutely require to get their jobs done; focuses on endpoints and resources more than just broad network segments; and uses network and application telemetry to modify security policy.