What the DOD and Intelligence Agencies Must Do on Cybersecurity
As a White House fact sheet notes, the memo “establishes timelines and guidance for how these cybersecurity requirements will be implemented, including multifactor authentication, encryption, cloud technologies, and endpoint detection services.”
For example, within 60 days, agencies that operate national security systems must update plans to “prioritize resources” for cloud computing and to implement zero-trust architecture.
Within 90 days of the date of the memo, the Committee on National Security Systems is required to develop and publish guidance “regarding minimum security standards and controls related to cloud migration and operations” for national security systems. And within 180 days, the covered agencies need to implement multifactor authentication and encryption for data stored in and moving across national security systems.
Agencies are also required to use NSA‑approved, public standards-based cryptographic protocols, and “if mission-unique requirements preclude the use of public standards-based cryptographic protocols, NSA-approved mission unique protocols may be used.”
RELATED: The shift to zero trust is about culture as well as technology.
Importantly, agencies must not authorize new systems to operate “that do not use approved encryption algorithms and implementations, absent an exception authorized by the head of an agency.”
Additionally, the memo requires agencies to secure cross-domain solutions, or tools that can transfer data between classified and unclassified systems.
“Adversaries can seek to leverage these tools to get access to our classified networks,” the fact sheet notes, and the memo “directs decisive action to mitigate this threat.” The memo requires agencies to create an inventory of their cross-domain solutions and directs the NSA to “establish security standards and testing requirements to better protect these critical systems.”
EXPLORE: How do granular identity and access management controls enable zero trust?
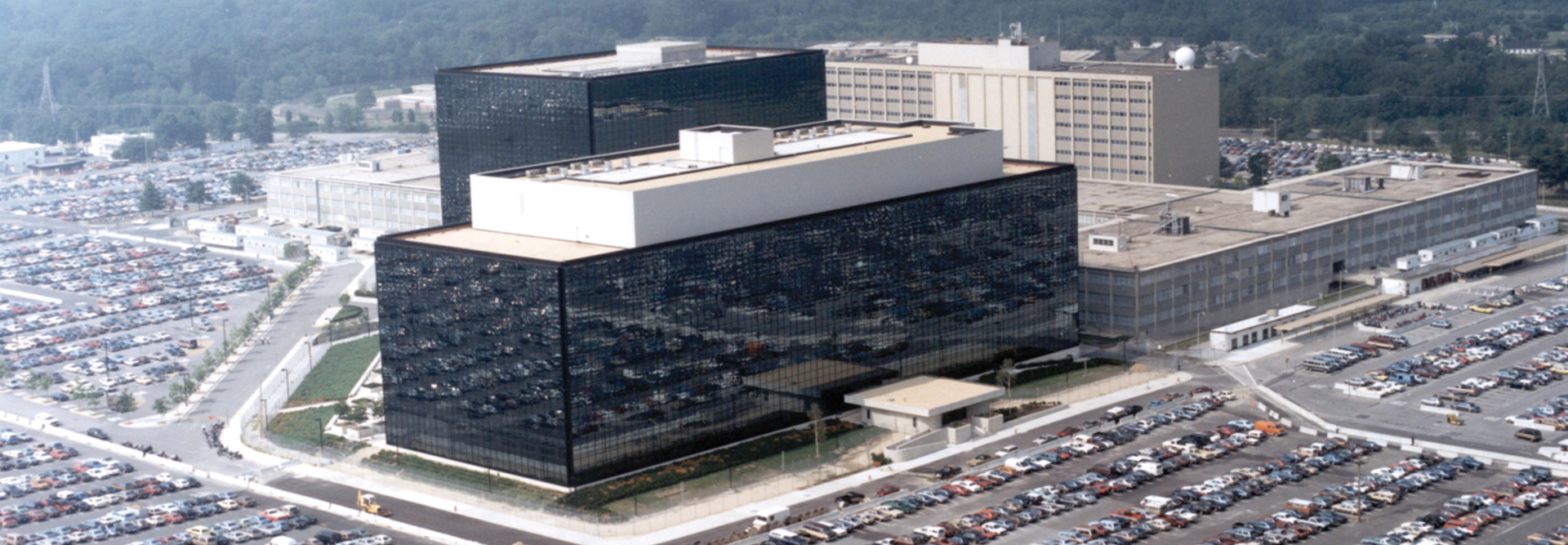
NSA Gets New Responsibilities and Authorities for Cyber
The memo clarifies that the NSA is the “National Manager” for the government’s classified systems.
Within 90 days, the NSA must, in coordination with the director of national intelligence, the directors of the CIA and FBI, and the heads of appropriate elements of the DOD, “develop a framework to coordinate and collaborate on cybersecurity and incident response activities” related to national security systems’ commercial cloud technologies to ensure effective information sharing among agencies.
The NSA also must coordinate with the Department of Homeland Security on cybersecurity incident management. The memo notes that DOD and intelligence agencies must identify their national security systems and report cyber incidents that occur on them to the NSA.
Significantly, the memo grants the NSA authority to issue binding operational directives on cybersecurity to protect the national security systems from or mitigate vulnerabilities from cyberthreats. That’s similar to the way DHS operates for civilian agencies. The memo “directs NSA and DHS to share directives and to learn from each other to determine if any of the requirements from one agency’s directive should be adopted by the other,” the fact sheet notes.