Federal Agencies Bolster Security by Streamlining IT
Agency IT leaders have long relied on a large collection of best-of-breed security products to effectively protect their networks.
While the approach provided adequate security, it was both expensive and difficult to manage. In recent years, however, CIOs and CISOs have begun to rethink their overall security philosophy with an eye toward consolidation.
“Instead of manually pulling together information and trying to detect events across numerous consoles, we can go to just one,” says Ralph Mosios, CISO for the Federal Housing Finance Agency (FHFA). “With all the information consolidated in one place, that gives us a fuller picture into our environment.”
For Mosios, consolidated-security architecture brought significant savings, helping him to purchase more capability at a lower cost. FHFA now uses a cloud-based, unified-threat management system that handles numerous security functions, including the firewall, intrusion prevention, anti-malware, content filtering and access control.
Mosios says the decision to utilize a multifunctional tool reduced the number of assets his team must maintain and update, decreased costs and increased staff productivity and flexibility.
“It just makes life a lot easier while also improving security,” he says.
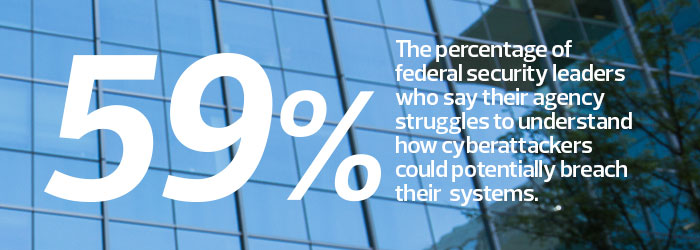 SOURCE: Source: (ISC)² and KPMG, “The State of Cybersecurity from a Federal Cyber Executive Perspective,” April 2016
SOURCE: Source: (ISC)² and KPMG, “The State of Cybersecurity from a Federal Cyber Executive Perspective,” April 2016
Simplifying Security
Mittal Desai, CISO at the Federal Energy Regulatory Commission (FERC), began to rethink his agency’s security architecture two years ago. While stand-alone toolsets provided adequate protection, they also added major manageability and overhead issues, says Desai, who added that he was sharing his perspective with FedTech and not necessarily the views of FERC.
Numerous tools and consoles increase the costs associated with product maintenance and personnel training. Stand-alone security tools can struggle to communicate with each other, at times making it difficult to pull data across the network. Communication becomes incredibly important when a network has become compromised, as administrators can review the data to find the exact point of infiltration.
Too many disparate tools can also hog bandwidth and cause network latency, which increases operational risk and user frustration.
“We saw more high-impact compromises and attacks across both agencies and corporations,” Desai says. “This prompted us to make investments to increase our visibility into and across the entire network.”
FERC plans to acquire several integrated, multifunctional and automated security toolsets that can help Desai and his team craft a more robust, seamless security architecture.
“We look for tools that can aggregate machine data created at our endpoints, whether it’s mobility, cloud-based services or internal infrastructure data, and put all that together into one central console,” Desai says. “We can analyze those events and filter those events for critical vulnerabilities and respond and mitigate that much more quickly and effectively.”
Streamlining the security architecture includes, at times, using multiple products from one vendor or from complementary products, including firewalls and multifactor authentication. The goal is to use products that work in harmony, as opposed to tools that work great on their own, but may not fit into the larger system.
New Solutions Improve Data Sharing
Moving to a more robust, seamless architecture has become easier because of the development of next-generation solutions, says Peter Firstbrook, vice president of research for Gartner.
Next-generation tools offer new capabilities, like data analytics and automation, which can help ease the workload and complexity for information security staff. Within the last year, some vendors, including Cisco Systems and McAfee, released product bundles that communicate and share traffic and alert information at a more meaningful level.
Firstbrook views these tools as potential game changers.
“Given the ability to integrate and exchange information, and to share their verdicts across different detection methods, these tools can actually improve security,” he says.
The Pentagon Gets Greater Security Visibility
Nowhere is the move to a robust, seamless security architecture more dramatic than the Department of Defense.
Pentagon IT leaders have spent several years defining and implementing the Joint Information Environment (JIE), a framework for IT modernization that, among other things, calls for a single security architecture across all military service branches and subagencies.
Jenine Patterson, the DOD’s division chief for cybersecurity portfolio management, says the JIE provides Pentagon IT staff greater visibility into the department’s networks. As such, IT staff can better organize security efforts across the architecture.
“Having a standards-based architecture and commonly equipped security tools allows us to better understand what information we need from our sensors,” Patterson says. “This provides those who need to take action during an emergency with the key information they need.”
Not surprisingly, creating the JIE has not been easy or quick.
DOD leaders have worked on the JIE framework since 2010. The complexity comes from the JIE’s need to enable a long-desired layered defense philosophy, with integrated security capabilities built at the network’s perimeter, mid-point, enclaves, endpoints and the data center — while still providing flexibility to users working close to the mission.
Defending One Network
Danielle Metz, who performs integration and strategy within the Office of the Deputy CIO for Information Enterprise, says DOD put much of its initial emphasis on defining and building out the Joint Regional Security Stacks.
JRSS serves as one of the bigger components of the single-security architecture, covering midpoint security capabilities like firewall functions, intrusion detection and prevention, enterprise management and virtual routing and forwarding.
The implementation of JRSS will result in the removal of approximately 1,000 midpoint security stacks from the agency’s unclassified and classified networks, bringing the total to 50.
A number of JRSS implementations have already begun at service branches. The more challenging steps that lie ahead, Metz explains, will be operationalizing JRSS as an enterprise service and collaborating with the different parts of the department on a common security platform.
“This is a shift in how we see and defend the cyberterrain,” Metz says.
In the end, JIE will save DOD money, reduce enemy attack areas and more effectively and efficiently pull together cybersecurity resources.
“The JIE is really an enterprise mentality,” Metz says. “It’s no longer, ‘I’m defending my own piece of the network and reporting out on how I’m defending it.’ We’re all defending the DOD network."