DHS Promises Coordinated Response to ‘Petya’/‘Nyetya’ Ransomware Attack
The Department of Homeland Security is monitoring reports of cyberattacks after computer systems worldwide were attacked by a new, virulent piece of ransomware.
The ransomware has spread to at least 65 countries, and has impacted businesses around the world, while cybersecurity researchers are so far unable to come up with concrete ways to stop the threat from spreading. The global cyberattack is not as widespread as the WannaCry attack that hit computers running Microsoft’s Windows operating system last month, but researchers say it is more sophisticated.
“The Department of Homeland Security is monitoring reports of cyberattacks affecting multiple global entities and is coordinating with our international and domestic cyber partners,” Scott McConnell, a department spokesman, said in a statement to The New York Times.
According to Reuters, DHS “advised victims not to pay the extortion, saying that doing so does not guarantee access will be restored.” The White House National Security Council said in a statement that the U.S. is investigating the attack but that there is currently no risk to public safety, Reuters reported, and the U.S. government is “determined to hold those responsible accountable.”
The ransomware appears to be a variant of the “Petya” malware Kaspersky Lab first reported in March 2016, The New York Times notes. In a blog post, Kaspersky says that the new malware “is significantly different from all earlier known versions of Petya, and that’s why we are addressing it as a separate malware family. We’ve named it ExPetr (or NotPetya — unofficially).” Cisco Systems’ Talos cybersecurity unit has identified the new variant as “Nyetya.”
The attacks take advantage of a vulnerability in Microsoft’s Server Message Block, similar to WannaCry. Microsoft issued patches for this exploit, but users who didn’t update their systems remained vulnerable. Moreover, because the Petya variant is a worm that can self-propagate, it can spread laterally across corporate networks even if other users patched their machines.
Speaking to reporters on Tuesday at the Cisco Live 2017 conference in Las Vegas, Craig Williams, senior technical leader and manager of Talos, said that the Nyetya attack is “significantly worse, significantly more virulent” than WannaCry and is much stealthier.
On Wednesday and Thursday, numerous cybersecurity researchers actually concluded that the attack was not even ransomware, but rather a piece of “wiperware” designed to wipe data from infected systems.
Matt Suiche, founder of the cybersecurity firm Comae, described the evidence behind that finding in a blog post. Kaspersky and Talos also confirmed it.
Vikram Thakur, technical director of Symantec Security Response, agreed with those assessments and said, “From just technical analysis we can say that this was actually designed as a wiping component rather than ransomware because parts of the data that should have been encrypted by ransomware, as one would imagine, were instead wiped.”
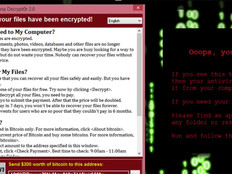
So far, although the attack has spread around the globe, it does not appear to have generated a great deal of ransom payments. Like WannaCry, the attack locks users out of their systems and files and demands a payment of $300 in the cryptocurrency bitcoin.
However, affected users should not pay the ransom. As ZDNet notes: “The email address displayed on the ransomware message has been blocked by the email provider, meaning nobody can get the decryption keys to unlock their computers.” That means, ZDNet added, that anyone who paid the ransom and “confirmed their payment to the email listed on the ransomware warning message wasted their money.” As of Wednesday morning, the Times reported, the address had logged 45 transactions.
The attack came a day before Ukraine celebrated its Constitution Day holiday, and Williams said the attack likely was intended to disrupt systems in the country. Ukraine’s national bank, state power company and largest airport were among the targets of the attack, The Independent notes.
Thakur says Symantec has known since the attack started that it was not actually financially motivated because it was spread first in Ukraine and targeted companies that did business with Ukraine. The attackers also must have known that the email address victims were supposed to send ransom payments to would have been shut down. So, who is behind the attack?
There could be a number of people, organizations or countries that could benefit from the attack, Thakur said. “We just don’t have enough information on that front to be able to conclusively say” who the attack’s mastermind is.
New Cyberattack Spreads Around the World
Microsoft said in a blog post that it “saw the first infections in Ukraine, where more than 12,500 machines encountered the threat. We then observed infections in another 64 countries, including Belgium, Brazil, Germany, Russia, and the United States.” Multiple security researchers, including Talos and Symantec, believe that the attacks started by cracking into MEDoc, a tax and accounting software package widely used in Ukraine. Symantec says in a blog post that MEDoc is “used for the initial insertion of Petya into corporate networks. MEDoc is widely used in Ukraine, indicating that organizations in that country were the primary target. After gaining an initial foothold, Petya then uses a variety of methods to spread across corporate networks.” According to Microsoft, there is “evidence that a few active infections of the ransomware initially started from the legitimate MEDoc updater process.”
Williams told reporters that the Nyetya malware spreads laterally via three attack vectors. One is a backdoor in EternalBlue, which as the Times notes, “was leaked online last April by a mysterious group of hackers known as the Shadow Brokers, who have previously released hacking tools used by the National Security Agency.” EternalBlue was the exploit used in the WannaCry attack. Talos and Microsoft say the malware also uses another exploit posted by the Shadow Brokers known as EternalRomance.
However, Nyetya also uses PsExec and the Windows Management Instrumentation tools to spread, according to Talos, Microsoft and Symantec.
“It’s also significantly more advanced than WannaCry, because WannaCry had one network vector,” Williams said. “This effectively has three. One utilizes the EternalBlue backdoor. The other two use username-and-password reuse on that system.”
The attackers in this case “were much more stealthy,” Williams said. Instead of shooting across the internet the way WannaCry did, this new attack “only moved internally and only moved laterally” inside infected systems. Several private companies said they were struck by the attack, according to the Times, including the American pharmaceutical firm Merck; the Danish shipping company AP Moller-Maersk; the British advertising firm WPP; French multinational Saint-Gobain; a unit of the bank BNP Paribas; the Russian steel and mining company Evraz; the Russian energy company Rosneft; and the American food company Mondelez International.
Williams said that any company that used the MEDoc software to pay Ukrainian taxes for Ukrainian employees that did not have their systems patched would have been exposed. Or if someone with a compromised system went on an unsecured network, he said, they could have spread the malware, since worms spread laterally from behind firewalls. “Anywhere you go, if you connect to an unsecured network, it can happen,” he said.
How to Respond to the Petya Attack
What should businesses do to inculcate themselves from the attack?
The first thing is to patch and update systems that have out-of-date security patches. Microsoft notes:
To protect our customers, we released cloud-delivered protection updates and made updates to our signature definition packages shortly after. These updates were automatically delivered to all Microsoft free antimalware products, including Windows Defender Antivirus and Microsoft Security Essentials. You can download the latest version of these files manually at the Malware Protection Center.
The second big step is to back up your data and make sure those backups are updated regularly and are kept off site. Users might say, Williams noted, “We thought we had backups, but when we looked the system hadn’t run since 2014, and you’re just saying, ‘Oh, God!’
“You have got to make sure you have backups; you have to test backups weekly,” he said. “And you have got to make sure they are not connected to the network and they can’t be erased.”
Thakur also stressed the importance of regularly checking backup systems. “That’s really everyone’s insurance at the end of the day," he said, “ where, not through your mistake but through somebody else’s mistake on the same network, something gets on your computer, at least you have it all backed up and can restore it.”
According to ABC News, Amit Serper of Boston-based Cybereason “identified a fix on Tuesday night, and other researchers have termed it a potential ‘vaccine’ or localized kill switch for the virus. By changing a single file name, Serper found, users can trick the malware into shutting down on their computers.”
However, while Serper’s method “has been confirmed by several other firms,” ABC notes, “he warned that it is only a temporary fix because large-scale attacks normally occur in several waves and hackers may easily change the file names, making the ‘vaccine’ ineffective.”
Williams noted that, for now, “there doesn’t seem to be an easy way around it.”