FEDTECH: From your vantage point, where have federal agencies made the most progress in their effort to adopt zero-trust architectures and where do they still have work to do?
TREXLER: Every customer is on its own journey when it comes to securing its environment, and that journey is constantly changing. New attack mechanisms emerge, new attackers appear, and agencies have to pivot to address the challenges of today and tomorrow, not yesterday.
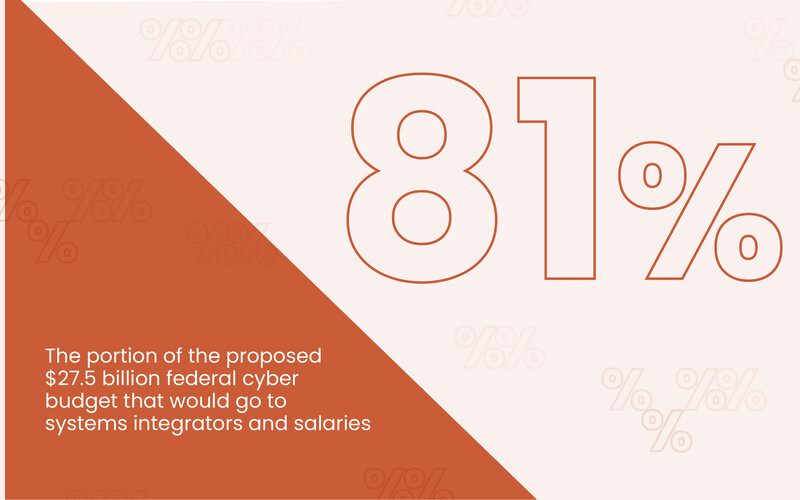
The government has spent a lot of time — and certainly a lot of money — on zero trust. Where we see the most progress is in identity. The FY 2025 proposed cybersecurity budget was about $27.5 billion for the federal government. It was never approved, but let’s call it $27 billion. Roughly $1.8 billion of that was in identity.
A number of organizations and agencies have made real strides in understanding who their workers are, what they do and what they should have access to. From our perspective, that’s one of the foundational components, if not the first stage, of a zero-trust strategy.
Beyond that, we’ve seen many organizations embark on the zero-trust journey and deploy technologies and capabilities that align with zero-trust principles. But there’s still a long way to go. These are the largest, most expansive organizations in the world. This is not a journey with a fixed destination, because the destination is constantly moving. The situation keeps evolving.
We’ve seen real progress — identity is a prime example, as are some SASE implementations and efforts to reduce permissions so people only see what they should see. But it remains an extremely complex, difficult journey that will take many more years.