“When we started this effort, Intune wasn’t very mature, but it’s made big strides lately,” he says. “We’re definitely taking a closer look at Intune, not only for its tighter integration with Office 365, but also for security benefits, such as conditional access controls for mobile apps.”
Adopting mobile device management at the same time that DHS is migrating to the cloud means asking agency employees to adapt to a lot of change over a short period of time.
“We’re throwing a lot at our users these days,” McCarty admits. “But the big benefit is that they now have an experience that’s more like they’re used to in their everyday lives, and they gain access to things they could never get to before on their mobile devices.”
MORE FROM FEDTECH: Discover how the Mine Safety and Health Administration has gone paperless.
SBA Provides Mobile Security for a Dispersed Workforce
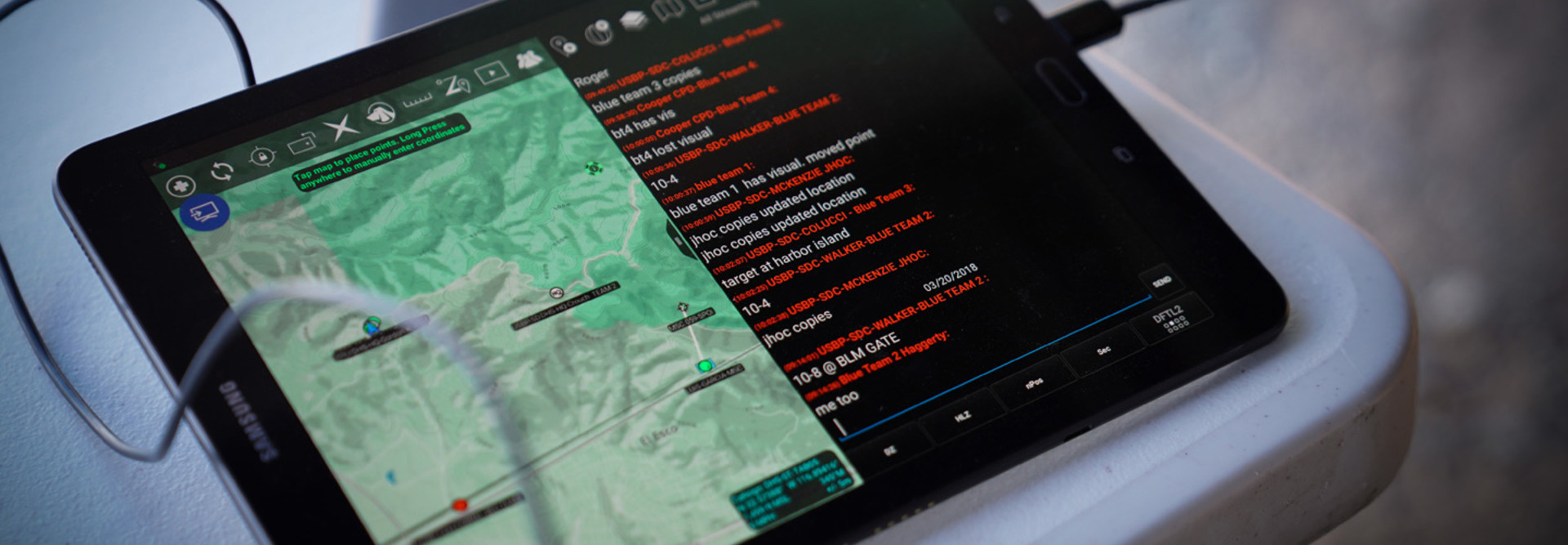
With more than 2,000 permanent employees spread across 128 locations, the Small Business Administration has a workforce that’s not only diverse but also dispersed. That’s why the SBA relies on 2,200 agency-issued smartphones and some 400 portable Wi-Fi hotspots to keep everyone connected.
Last year, the SBA moved from using only iPhones running on the AT&T network to a mix of iOS and Samsung Galaxy devices across the three major U.S. carriers, says Russ Miller, director of IT services. That allowed the agency to maximize coverage in remote areas not served by AT&T, as well as to run internal apps that were not iOS-compatible.
The SBA also migrated from IBM MaaS360 mobile device management software to Microsoft Intune, and added Zimperium mobile device security to protect against malicious apps.
“We had a small library of apps our employees could access, but Zimperium let us enlarge that a bit more because it blocks the viruses and malware that can come with rogue apps,” he adds. “If you allow people to download any application they want, you open yourself up to a host of vulnerabilities and risks.”
Using Intune allows SBA employees to securely access their Microsoft OneDrive accounts, which lets them read and edit files stored in the cloud from their phones.
“That can be risky,” he adds. “But if you have the right security software on the phone, you can always remotely lock or wipe the device. If it gets lost or stolen, it’s a brick — it can’t be used.”
MORE FROM FEDTECH: See how the Air Force secures and customizes its mobile solutions.
USDA Evolves Its Approach to EMM
Miller says EMM software has evolved a great deal since the first solutions appeared.
“Seven or eight years ago, most of the device management tools didn’t let you lock the device or secure the data you had on it,” he says.
“Today, if someone leaves the agency and has password-protected their device, we have to throw the phone away — even Verizon or AT&T wouldn’t be able to clear the device so we could reuse it.”
Like DHS and SBA, the Agriculture Department has a mixed mobile environment, with more than 90 percent of its 32,000 government-issued mobile devices using iOS. And like those agencies, the USDA’s biggest security concerns center on application-based threats, says Frank Chad Hoeppel, acting associate CIO for the USDA’s Client Experience Center.
.jpg)
USDA Animal and Plant Health Inspection Service Plant Protection and Quarantine technicians Bethany Benedict and Brendon Miller inspect an adhesive band used to sample insects in the area. The number of insects of interest that are stuck to the band are identified counted and the data is entered into a smart tablet. Photo credit: Lance Cheung/USDA
The USDA has used MobileIron since 2013 to manage the devices, alongside Symantec-owned Appthority to screen apps for potential malware or vulnerabilities.
The department is currently implementing blacklisting and whitelisting capabilities to create a roster of third-party apps approved for business use, as well as finalizing its BYOD policies, Hoeppel says.
“Five years ago, our mobile program provided email access to mobile devices,” Hoeppel says. “Today, using mature EMMs, we securely manage devices and provide a flexible suite of productivity applications to our employees, allowing them to work anytime, anywhere.”







.jpg)




