Agencies Get Unified and Simplified Security
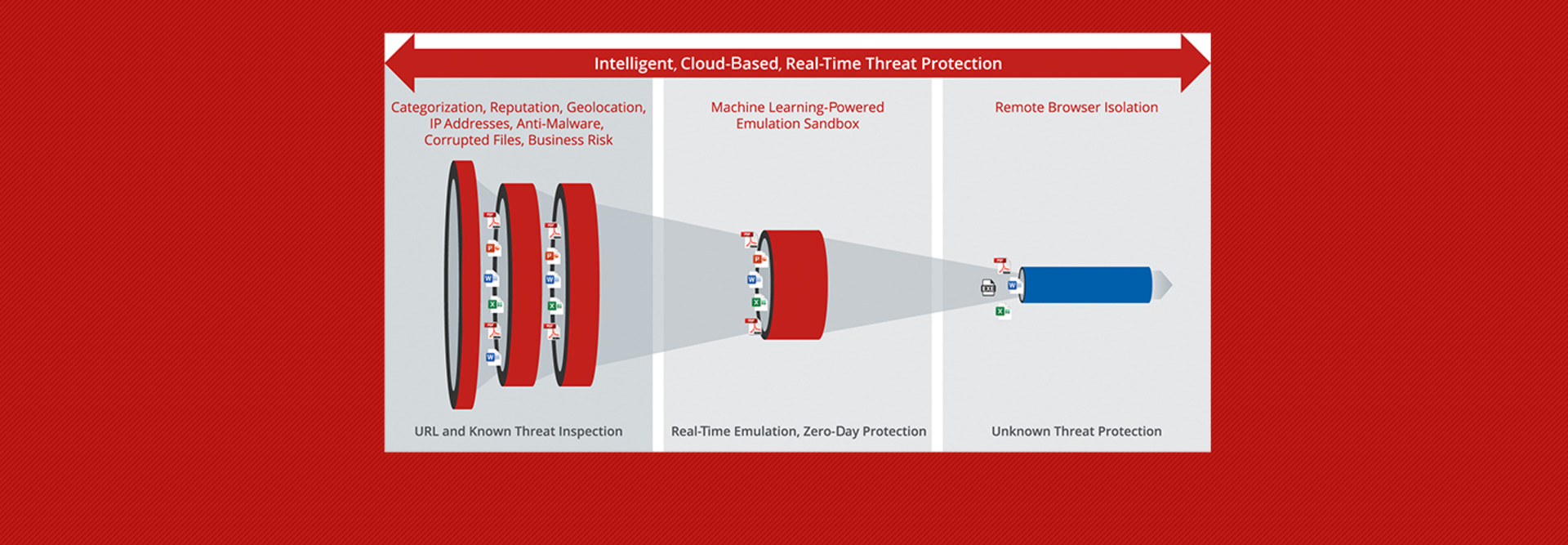
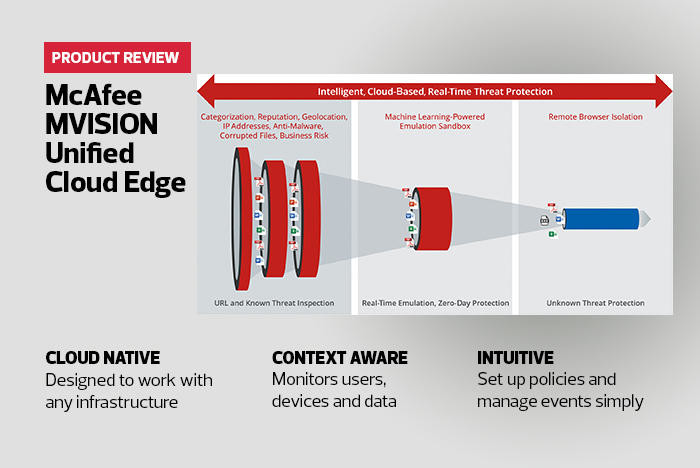
At the heart of the UCE platform is the MVISION console. It acts as a cloud access security broker, a secure cloud gateway, an endpoint protection platform, a data loss prevention tool and more. I mostly tested the cloud access capabilities, although the rules I created could also apply to the rest of the infrastructure as well.
The UCE platform was surprisingly easy to manage despite the complexity of the demo environment where it was being tested. As a test, I was able to apply a security policy to any application that used the Mail.ReadBasic scope.
Once the new rule was in place, the dashboard showed me how many apps were affected.
Because the UCE is context-aware, I could set up automatic actions based on almost any situation. For example, I could set one policy for a valid user on a personal device and another for a valid user on a company-owned resource. Some of the many actions available included revoking access, forcing users to interact via an isolated browser or forcing a security update.
A Bridge to Zero-Trust Security
Because the McAfee UCE is contextually aware and administrators can finely tune access and permissions, it provides a bridge to a zero-trust environment — an environment that federal cybersecurity experts are insisting on.
At least for cloud applications, federal agencies can tap the UCE to provide the most robust zero-trust protection possible in today’s increasingly dangerous threat environment.