How Has the Government Shutdown Impacted Federal IT?
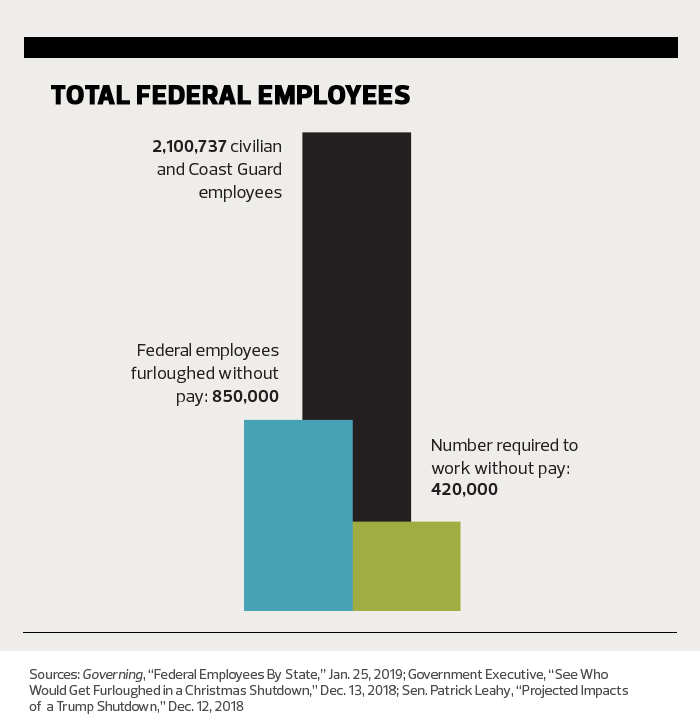
From unpaid workers to unavailable services, the short-term impact of the longest federal government shutdown in history was obvious. But in the long term, the aftereffects may be more problematic.
FedTech magazine asked a panel of former federal IT leaders to discuss the impact of the shutdown. These experts, now in academia, consulting firms and tech companies, still work with the federal government in their various capacities.
Our roundtable consisted of Jonathan Alboum, former CIO of the Department of Agriculture, now with Veritas Technologies; Steve Grewal, former General Services Administration deputy CIO, now with Cohesity; Jerry McGinn, former senior Defense Department official, now executive director of the Center for Government Contracting at the George Mason University School of Business; and Theresa Payton, former White House CIO, now CEO of Fortalice Solutions.
Alboum, Grewal and McGinn served in the Obama and Trump administrations; Payton worked for President George W. Bush. They all share their unique perspectives on how the most recent shutdown affected — and may continue to affect — IT modernization projects, procurement, cybersecurity and contracting.
MORE FROM FEDTECH: Find out what digital twin technology is and how agencies can use it.
FEDTECH: What impact did the shutdown have on the deployment of new technology and programs?
ALBOUM: Modernization projects normally aren’t considered essential services. And when there’s a shutdown, people who work at government contractors are often furloughed like government employees. They don’t have guarantees of back pay and will look for new positions. I know some circumstances where contractors ended up leaving their current contract for another contract that was funded. When government employees returned and tried to resume work, they came back to teams that didn’t have the same staffing levels. Having to hire people again for key positions is disruptive.

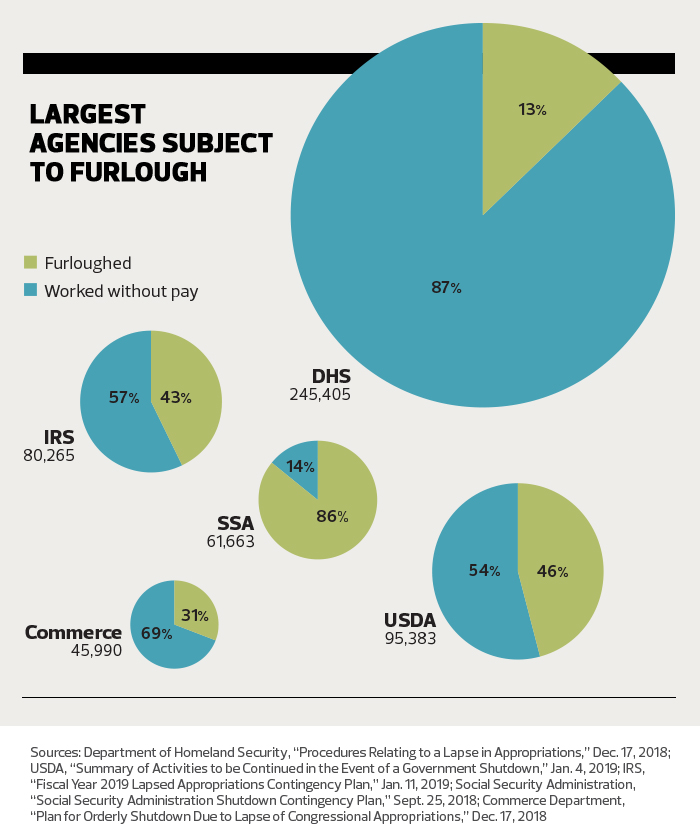
PAYTON: Not only did the shutdown leave us open to cyberattacks at home and around the globe, it put progress on hold, and, in some cases, undermined it. For example, in November, Congress approved the new Cybersecurity and Infrastructure Security Agency at the Department of Homeland Security. CISA is just getting off the ground. Running at full speed requires a lot of work and resources, but, according to guidance, nearly 40 percent of CISA’s staff was furloughed during the shutdown.
MORE FROM FEDTECH: Find out how federal IT leaders can adapt to accelerating technological change.
FEDTECH: What is the ripple effect on technology-related contractors and vendors?
PAYTON: Even among those contractors and vendors whose work was considered essential, some were not able to continue working because their government counterparts were nonessential and weren't there to direct the work. The unpredictability of shutdowns puts extreme pressure on companies and could lead to layoffs.
McGINN: The impact is significant. Companies were putting their employees in training activities or encouraging them to take leave or use their vacation time, so they didn’t have to lay them off. Big companies could handle it better, but if you’ve got a small, 100-person shop, and 80 percent of your revenue comes from a contract and your client gets furloughed, can you imagine trying to make payroll when you’re not getting paid? Companies were losing tens of thousands of dollars a day.
FEDTECH: What is the impact on cybersecurity when fewer workers are available to watch for problems?
GREWAL: It definitely generates a blind spot and increases the risk posture for government. When I was CISO at the Department of Education, during the 2013 shutdown, we were successful in having some security personnel in the security operations center deemed essential, so they could continue to work. But from a macro context, if we look at government as a whole, it does leave us in a more vulnerable state not having full-time security resources and expertise across the board.
PAYTON: Shutdowns inevitably have consequences if short-staffed agencies have to make decisions about which IT and cybersecurity functions to staff during a shutdown. We faced several potential shutdowns from 2006 to 2008 while I was serving as CIO for the Executive Office of the President at the White House. Thankfully, we never had to execute those plans. But I can tell you that just focusing on a shutdown creates a diversion from the mission and diminishes critical momentum.
MORE FROM FEDTECH: Find out the keys to achieving digital transformation in government.
FEDTECH: What happens when the procurement process is interrupted for that length of time?
McGINN: It disrupts the normal course of business. You are not able to start new contracts. And if you are in the middle of a procurement, the whole selection process will stop. It will be delayed.
ALBOUM: You are creating quite a long backlog when work resumes. That’s because everything gets reprioritized. The thing at the top of the queue may no longer be at the top of the queue.
GREWAL: Procurement activities come to a screeching halt, with the exception of any mission essential actions.
PAYTON: The government procurement process requires coordination between procurement officials and cybersecurity subject matter experts in government. The preprocurement phase alone, consisting of market research and security requirement generation, can take up to a year or more. When work is essentially stopped, the queue increases and people who are already busy have that much more to do upon their return.
FEDTECH: What is the impact on data collection, backup and archiving, as well as dashboard updates and other projects that involve regularly collected and updated information?
PAYTON: From our perspective, routine data collection, backup and archiving and other functions deemed mission-essential were likely not impacted by the shutdown. Now, dashboard updates and longer-term projects — those are the items that have been impacted, and it will mean that the nation is stalled in implementing important new capabilities for fighting cybercrime.

ALBOUM: Data collection pauses during a shutdown. The public may submit data, but no one is collecting it, creating a big backlog. In my opinion, archiving and data protection are essential and should continue irrespective of a shutdown. In some environments, things like data protection may fall by the wayside because their importance isn’t fully appreciated.
MORE FROM FEDTECH: Discover how AI will reshape the federal workforce.
FEDTECH: Did automation or artificial intelligence play any role in keeping operations running during the shutdown?
GREWAL: It’s still in the early stages in government. If we think about robotic process automation, where you take a series of tasks and automate them, or if you think about automated response actions in cybersecurity, there are some elements of that. But those capabilities are not fully mature. Overall, it’s still a light footprint.
ALBOUM: I know of one agency that invested in robotic process automation and had bots running during the shutdown, so some operations continued. It was in financial management — processing invoices and paying bills. That was a benefit to them, and taught them some valuable lessons about RPA.
FEDTECH: How long should it take the government to be fully up and running again?
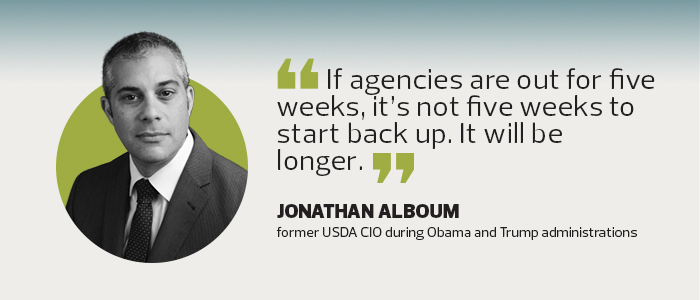
ALBOUM: If agencies are out for five weeks, it’s not five weeks to start back up. It will be longer, especially as there will be workforce issues with contractors. Five weeks can translate to eight weeks or more.
GREWAL: It’s a challenging question because of the size, scope and complexity of the mission areas for each federal organization. It’s not one-size-fits-all. If you have a government-owned, government-operated model, and you are able to deem certain IT operations’ components mission-critical, you can probably get back to operational quicker because you are less dependent on federal personnel other than oversight functions. With vendors and contractors, you have to go back and issue modifications around procurement and issue some correspondence around resuming operations, so it may not be as quick of a ramp-up.
There is also a reporting exercise that takes place, where the Office of Management and Budget requests an impact assessment to get metrics on what we delivered as the U.S. government and what things we could not respond to or act on. For example, when we were shut down, how many grant-related requests did we not respond to? Day one of resuming operations is not always day one of actually picking up where you left off. There are other administrative exercises that take place, so you have more of a lag before you get back to where you left off.
FEDTECH: What long-term impact do you see from the shutdown when it comes to technological issues?
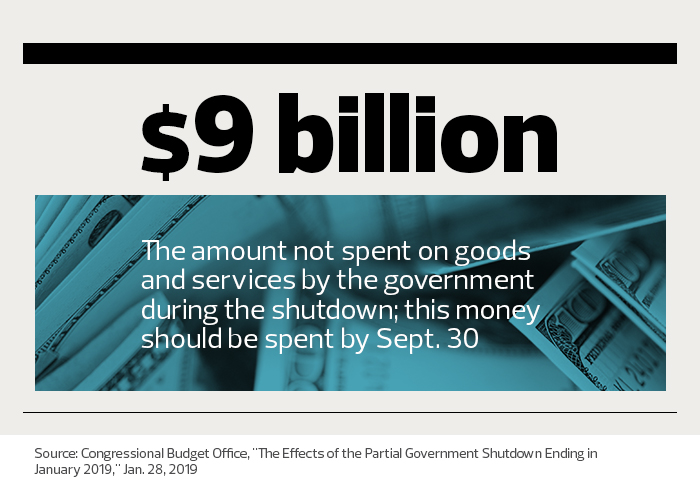
GREWAL: What concerns me most is the lost time. If you take on the post-shutdown activities we talked about, there are organizations that are behind for a couple of months. The long-term impact is the lack of deliverables in some areas that were planned for this fiscal year.
As we have quarterly delays and fiscal year delays, it will be hard to recover from that. You may have funding that expires. The only way to catch up is to throw additional resources at the problem, meaning more people and money. I think we will continue to feel the impact of the shutdown for the foreseeable future where there is no additional resourcing.
PAYTON: The long-term impact is not necessarily loss of capabilities against cybercrime, it's more of a delay in implementing enhanced capabilities. It means that projects can be delayed for months as the government gets up to speed and prioritizes the work that did not get done during the shutdown, plus incoming work.

FEDTECH: What technology-related lessons can agencies take away from the shutdown?
PAYTON: The best lesson is to be prepared for shutdowns. Expand the definition of mission-essential from core operations to include longer-term projects and initiatives that are equally as mission-essential and aimed at keeping the nation on the cutting edge of defending against cybercriminals.
McGINN: It is critical for government and industry to find ways to make the government more responsive and efficient. There are a number of important initiatives underway around how we can encourage innovation and get new entrants in the government contracting space, such as more Silicon Valley companies. We need to accelerate these efforts. If government runs better, there’s less reason to create future budget battles that lead to shutdowns.
GREWAL: If we are better able to leverage automation and AI, it will naturally minimize the impact of future shutdowns.
ALBOUM: It’s also very important that systems, network and data protection — all these operational capabilities — are well documented. In a situation where you have to work with a reduced staff, you can’t have the knowledge in the heads of a few people. It has to be extendable to the rest of the team.











