NIST also updated its Cybersecurity Supply Chain Risk Management Practices for Systems and Organizations (Special Publication 800-161 Revision 1), which provides best practices for agencies to identify, assess and mitigate cybersecurity risks throughout their supply chains.
Jon Boyens, deputy chief of NIST’s computer security division, says the updated guidance will help agencies implement cybersecurity supply chain risk management (C-SCRM). “It is a big document, but we wanted to put it all in one place for the different stakeholders, whether you’re a contracting officer developing a system, an operational information security person or in the CIO shop developing policies,” he says.
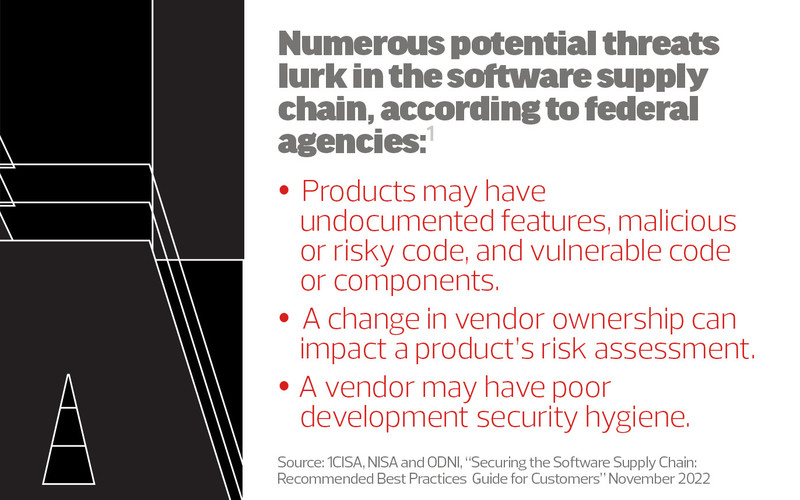
In a complementary effort, CISA, NSA and the Office of the Director of National Intelligence (ODNI) have recently published three guidelines for software developers, suppliers and customers. For customers, such as government agencies and private sector companies, the guidance covers recommended best practices from procurement and deployment to operations.
EXAMINE: How to keep federal supply chains resilient and secure.
The Importance of Supply Chain Security
In the federal sector, supply chain security is critical because the government’s day-to-day operations are increasingly digitized and software-based. With agencies and the private sector doing a better job of securing their perimeters, threat actors are forced to find vulnerabilities in the supply chain that allow access into organizations, Boyens says.
For example, the Log4j vulnerability caused a massive security crisis worldwide when it was discovered in December 2021. Log4j, a popular open-source Apache logging framework, is widely used in enterprise and web applications.
“Supply chain security is a high priority because – as you’ve seen in the latest published attacks of Log4j and SolarWinds – open-source and commercial components can include substantial and far-reaching vulnerabilities,” says Carol Lee, director of the NSA’s Center for Assured Software.
The software supply chain encompasses everything needed to produce software, from custom code, open-source software and cloud services to developers and DevOps teams. So, the supply chain not only includes the finished product, but also components developed elsewhere.