FITARA in 2018: The Tech and Policies Agencies Need to Comply
Within the next few months, the House Committee on Oversight and Government Reform will likely issue a new round of report cards that grade agencies’ compliance with the Federal Information Technology Acquisition Reform Act.
Agencies are being graded on more components of IT modernization under the law than ever before, with software license management, CIO reporting structure, cybersecurity solutions and other factors all under assessment.
There are both technology and policy tools agencies can use to boost their grades on the FITARA scorecards and enhance their FITARA implementation, according to government technology experts. Moreover, they say, as agencies’ IT modernization tasks grow more complex, the FITARA scorecards — along with input from other sources, such as the federal CIO Council — will serve an important role in increasing the transparency of agencies’ efforts, allowing them to learn from each other.
“I think it is extremely important that agencies are transparent about their performance, that they continue to improve and that they continue to share best practices with one another,” says Mallory Barg Bulman, vice president of research and evaluation at the Partnership for Public Service. “The government is one enterprise, and each agency has similar challenges — outdated technologies, an aging federal workforce. A tool like the FITARA scorecard allows for some benchmarking across government.”
VIDEO: See how USCIS and SBA evolve their website services with emerging technology!
What Is FITARA?
Congress passed FITARA as part of the National Defense Authorization Act for Fiscal Year 2015, and President Obama signed it into law in December 2014. As the Office of Management and Budget notes, FITARA represented the first major overhaul of federal IT in almost 20 years, following the passage of the Clinger-Cohen Act in 1996.
“FITARA is important because it serves as the seminal legislation on how agencies should improve their IT acquisitions and operations,” says Carol Harris, director of IT acquisition management issues for the Government Accountability Office. “It lays out in very basic terms where the greatest gains can be obtained.”
The law has many provisions, but its main goal is to strengthen the role of agency CIOs by requiring numerous agencies to have their CIO play a significant role in IT decisions, including annual and multiyear planning, programming, budgeting, execution, reporting, management, governance and oversight.
FITARA requires CIOs to certify that IT investments are adequately implementing incremental development. OMB has required agencies’ investments to deliver functionality every six months.
Additionally, FITARA requires OMB to publicize detailed information on federal IT investments and requires agency CIOs to categorize their major IT investments by risk.
FITARA was also designed to spur cost savings from IT investments. The law requires OMB to develop (and most agencies to implement) a process to review IT investment portfolios in order to boost efficiency and effectiveness, and identify potential waste and duplication. OMB is required to develop standardized performance metrics and to submit a quarterly report to Congress on cost savings.
FITARA also requires agencies to give OMB a data center inventory, a strategy for consolidating and optimizing data centers (now under the auspices of the Data Center Optimization Initiative) and quarterly progress reports. The law also requires OMB to develop a goal for what should be saved through this initiative and provide annual updates on the cost savings that are achieved.
What Are the Newest Elements of the FITARA Scorecard?
With GAO, the House Committee on Oversight and Government Reform developed a biannual scorecard to measure agencies’ progress toward meeting the requirements of FITARA, assigning them letter grades. The latest report cards were issued in May, with 11 of 24 agencies receiving lower grades since the last scorecard was released in November 2017.
Over the past few years, more elements have been added to the report cards. In addition to measuring progress on agency CIO authority enhancement, transparency and risk management, portfolio review and the DCOI, Congress has passed new laws that have become components of the FITARA scorecards.
In July 2016, President Obama signed into law the Making Electronic Government Accountable By Yielding Tangible Efficiencies Act of 2016. The law, better known as the MEGABYTE Act, requires agency CIOs to develop a comprehensive software licensing policy. Further, starting fiscal year 2017 and continuing for the next five fiscal years, CIOs must submit to the director of OMB a report that details the financial savings or avoidance of spending that has resulted from improved software license management.
Under the MEGABYTE Act, agencies are required to create a comprehensive, regularly updated inventory of software licenses and analyze software use to make cost-effective decisions.
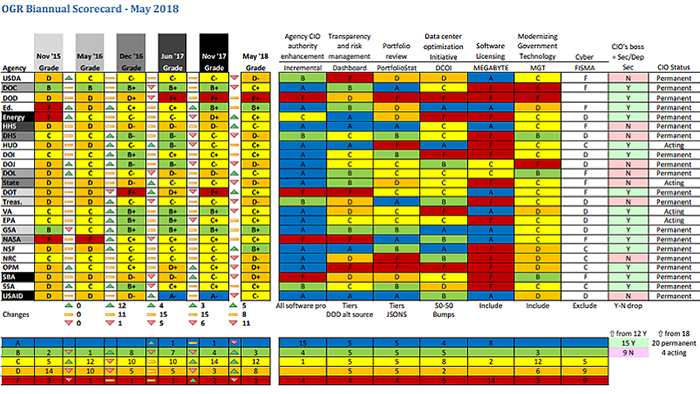
The latest FITARA scorecard grades, issued in May 2018.
Under the scorecard, an agency receives a grade of C if it has a comprehensive, regularly updated inventory of software licenses. Those agencies receive an A if their inventory is used to make cost-effective decisions.
In December 2017, President Donald Trump signed the Modernizing Government Technology Act into law. The IT modernization legislation, passed as an amendment to the 2018 National Defense Authorization Act, is designed to spur agency migration to the cloud, shutter legacy systems and allow for investments in new technologies.
The MGT Act authorized agencies to create internal working capital funds to reprogram their IT budgets and fund modernization projects. Each agency has its own technology priorities, and it will likely take some time for the law to bear fruit. The law also created a centralized Technology Modernization Fund.
An agency receives an A if it has an MGT-specific working capital fund with a CIO in charge of decision-making; a B if it plans to set up an such a fund in 2018 or 2019; a C if it has a department-level working capital fund; a D if it has some other IT-related funding method; and an F otherwise.
Finally, in the latest FITARA scorecard, the committee previewed a new item that will be added moving forward related to cybersecurity. Congress enacted the Federal Information Security Modernization Act of 2014 in December 2014 to improve federal cybersecurity and clarify governmentwide responsibilities.
FISMA is intended to promote the use of automated security tools that are able to continuously monitor and diagnose the security posture of agencies and provide for improved oversight of their information security programs. In particular, the act clarifies and assigns additional responsibilities to entities such as OMB and the Department of Homeland Security.
The scorecard area combines agencies’ inspector general federal assessments and self-reported cross-agency priority cybersecurity goals that are part of the President’s Management Agenda. IG assessments and CAP goals each account for half of the grade.
MORE FROM FEDTECH: Find out how agencies can overcome technical debt and replace legacy systems!
Why Is FITARA Important for Federal IT Leaders?
Bulman notes that one of the benefits of a transparent and open scorecard is that agencies know what they are being scored on and they can see how other agencies are performing.
That benchmarking is “powerful,” she says, because it allows agencies to learn from each other, especially those that are scoring well.
Harris adds that the CIO Council helps with that; and that GAO, through its reports on initiatives such as DCOI, software licensing, portfolio review and more, also helps agencies identify and share best practices.
The House Committee on Oversight and Government Reform's subcommittee on IT held a hearing on May 23, 2018.
The Trump administration has made IT modernization one of the key elements of its agenda, and is putting pressure on agencies to move faster to modernize IT architectures, adopt the cloud and empower their CIOs.
In addition to FITARA, in May Trump signed an executive order that requires CIOs at CFO Act agencies to report directly to the head of their agency and gives them voting powers on “bureau-level IT governance boards,” a greater say in the hiring of IT talent and more influence in shaping the enterprisewide vision of their agency’s technology infrastructure.
The FITARA scorecard, Harris says, serves a “one-stop shop in terms of where the individual agencies are, from a comprehensive perspective, on their IT hygiene,” including those CIO reporting structures.
How Can Agencies Comply with FITARA?
How can agencies boost their grades? In some cases, simple changes to IT governance might be sufficient. Harris notes that in the last round of FITARA scorecards, the biggest penalties were for agencies whose CIOs did report directly to their agency heads (nine agencies do not have CIOs reporting to the agency secretary and 15 do, up from 12 in the previous round).
The importance of CIO reporting is not new, Harris says, noting that FITARA only reinforced what had been introduced in Clinger-Cohen.
In terms of managing software licenses under the MEGABYTE Act, agencies can use automated software asset management tools to improve their grades, Harris says. There are numerous SAM tools on the market, including those from Snow Software and Ivanti.
“That regular update of the inventory — and doing it systematically, in an automated fashion through a tool — is something that agencies could benefit from,” she adds, but notes that the tools will not provide agencies with a 100 percent completed software license inventory.
“What’s more realistic and reasonable would be for agencies to cover 80 percent of the inventory that they have, and then from there, regularly update and analyze for software use to make those cost-effective decisions,” Harris says.
Agencies can also continue to boost their scores under the Data Center Optimization Initiative through automated tools that monitor data center efficiency, says Harris. In addition to requiring agencies to house at least four virtual servers per physical server and achieve a server utilization rate of at least 65 percent, DCOI also requires agencies to install energy metering tools in all tiered data centers to measure power consumption, and maintain a power usage effectiveness score of less than 1.5 (preferably, less than 1.2).
To meet the FISMA requirements, agencies need to ensure that they are “effectively implementing a comprehensive information security program,” Harris says. Automated security monitoring tools are one element of that strategy, she notes. Agencies need to complete information security policies on an enterprisewide basis and put those into action, she adds.
“The focus is really on the management side of things, as opposed to the technology and the tools they can use,” Harris says. “That’s one very important element, but again, there are many ways agencies can go about fulfilling the expectations and goals set out in those plans. It’s really on them to identify what is best for them from a business perspective.”